Содержание
- 2. Chapter 5 –Advanced Encryption Standard "It seems very simple." "It is very simple. But if you
- 3. AES Origins clear a replacement for DES was needed have theoretical attacks that can break it
- 4. The AES Cipher - Rijndael designed by Rijmen-Daemen in Belgium has 128/192/256 bit keys, 128 bit
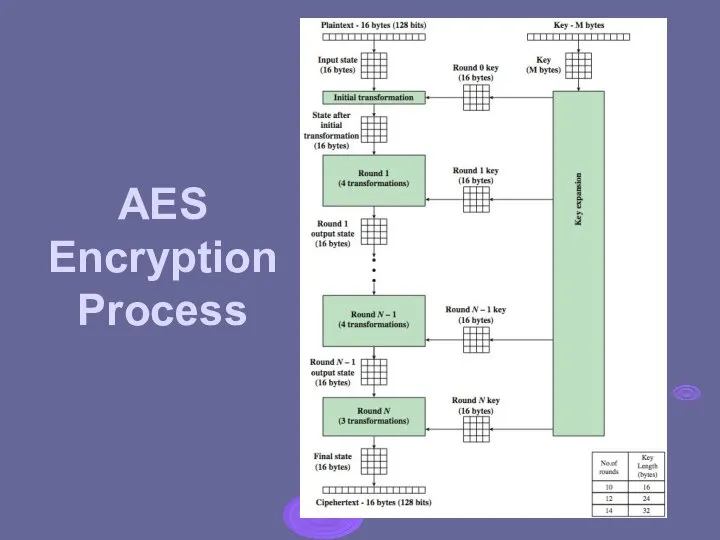
- 5. AES Encryption Process
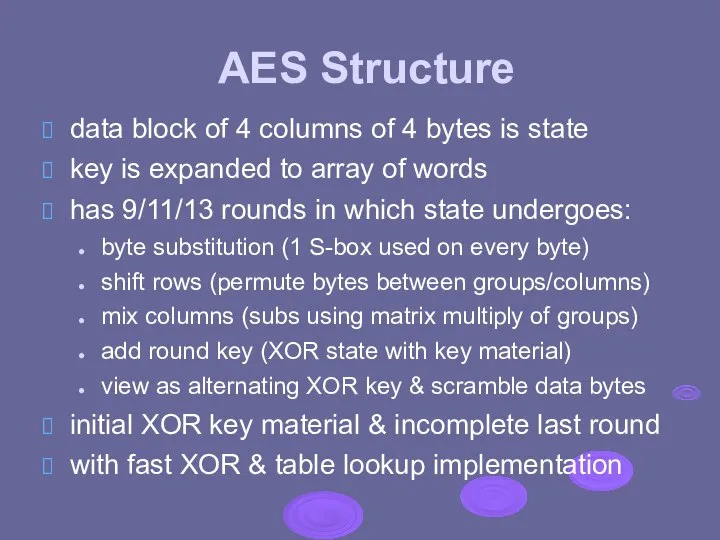
- 6. AES Structure data block of 4 columns of 4 bytes is state key is expanded to
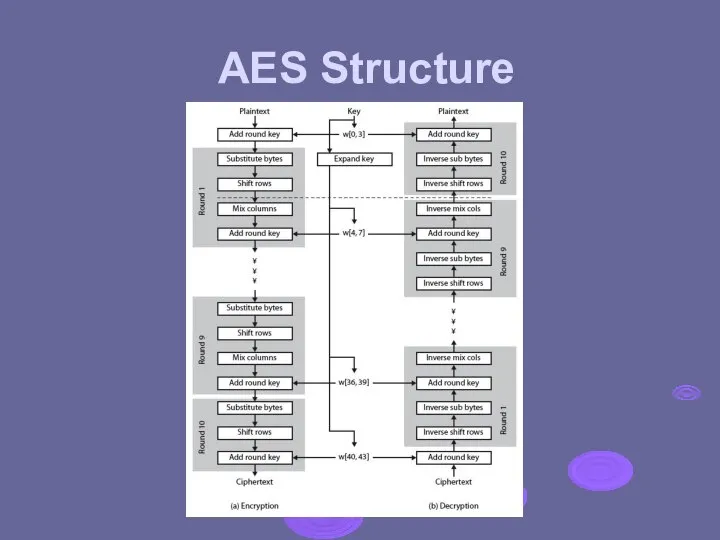
- 7. AES Structure
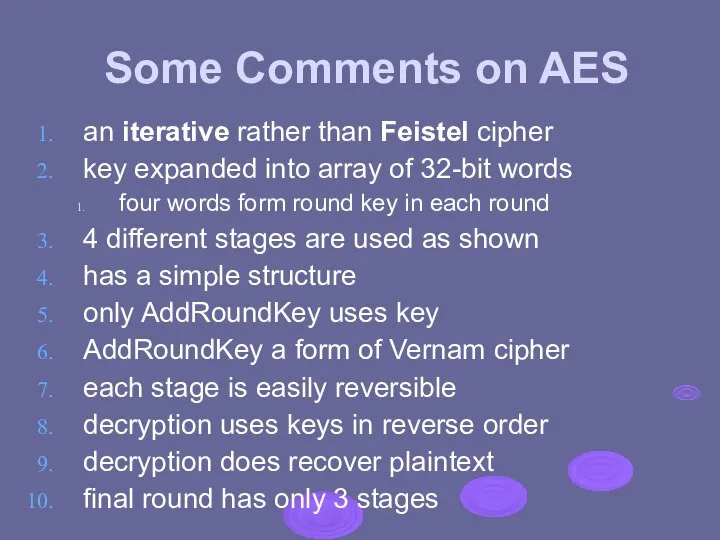
- 8. Some Comments on AES an iterative rather than Feistel cipher key expanded into array of 32-bit
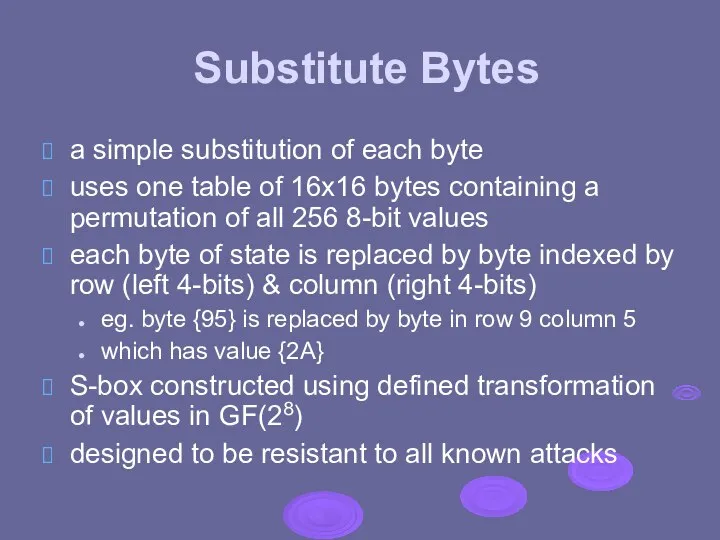
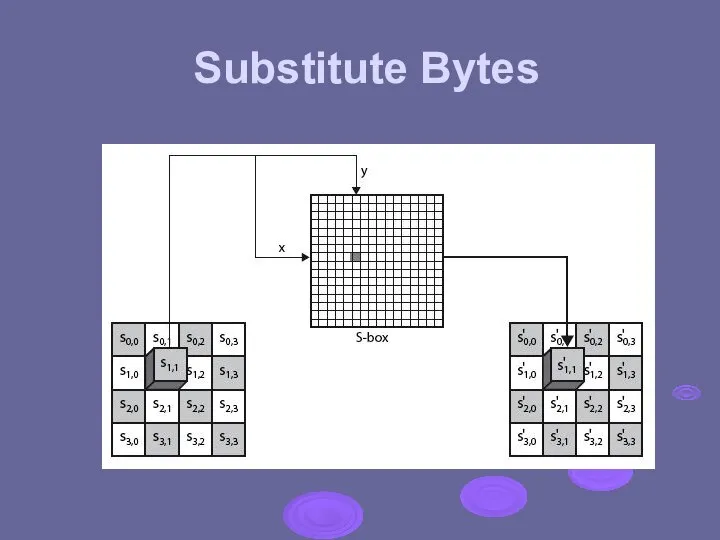
- 9. Substitute Bytes a simple substitution of each byte uses one table of 16x16 bytes containing a
- 10. Substitute Bytes
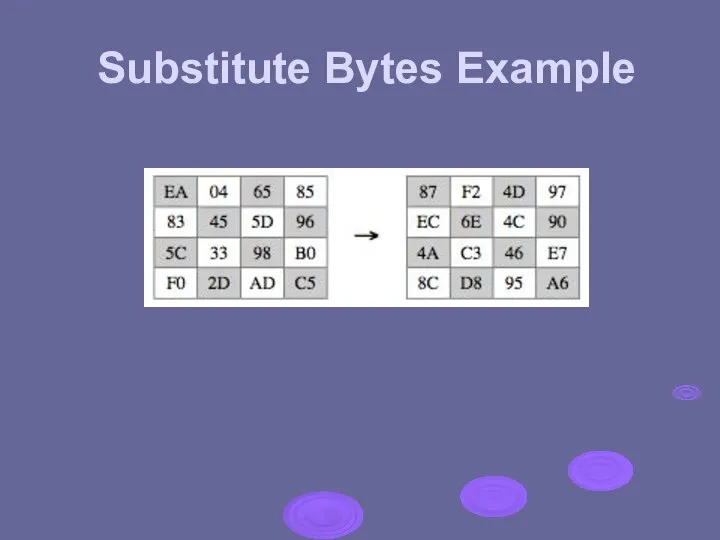
- 11. Substitute Bytes Example
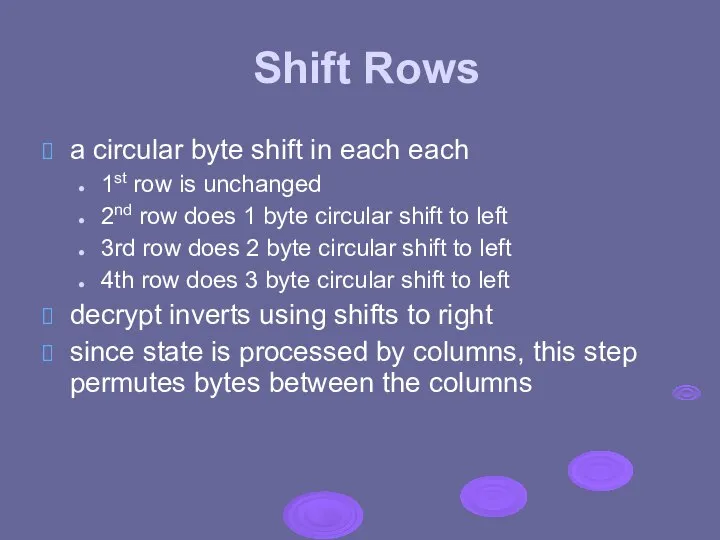
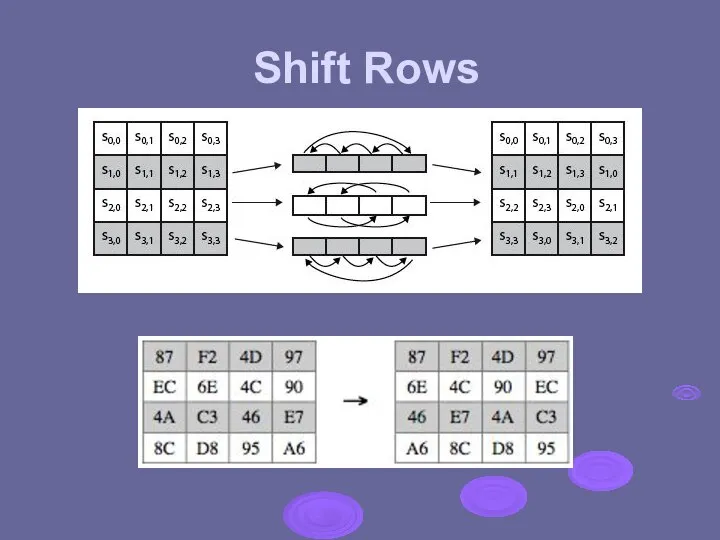
- 12. Shift Rows a circular byte shift in each each 1st row is unchanged 2nd row does
- 13. Shift Rows
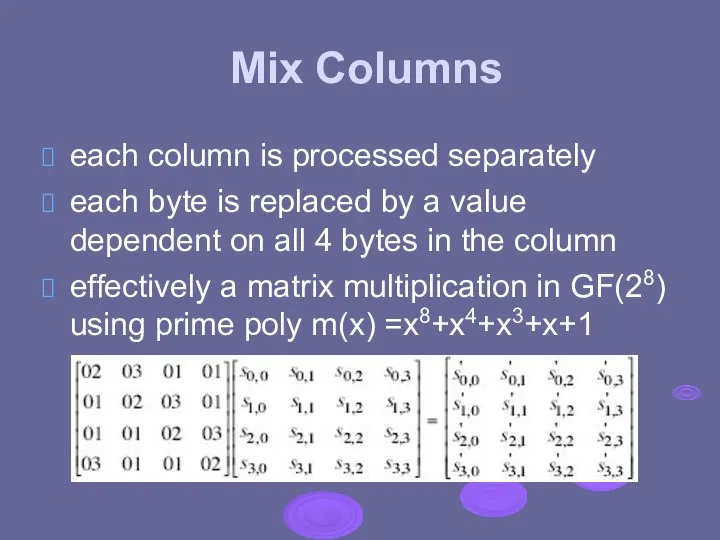
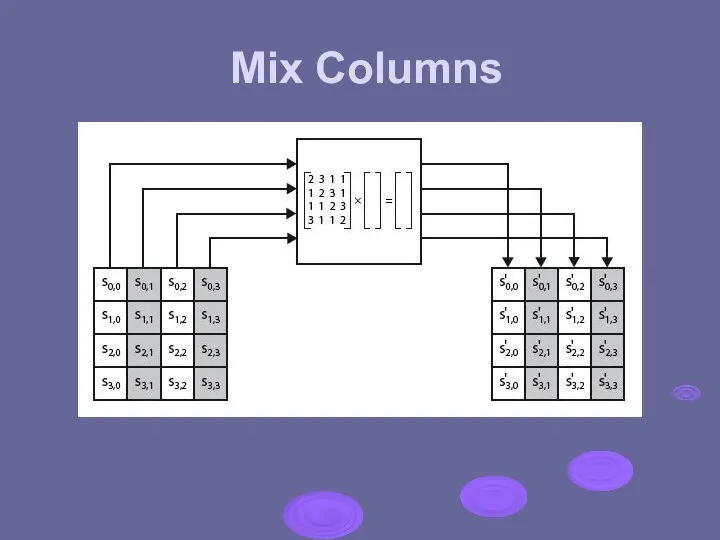
- 14. Mix Columns each column is processed separately each byte is replaced by a value dependent on
- 15. Mix Columns
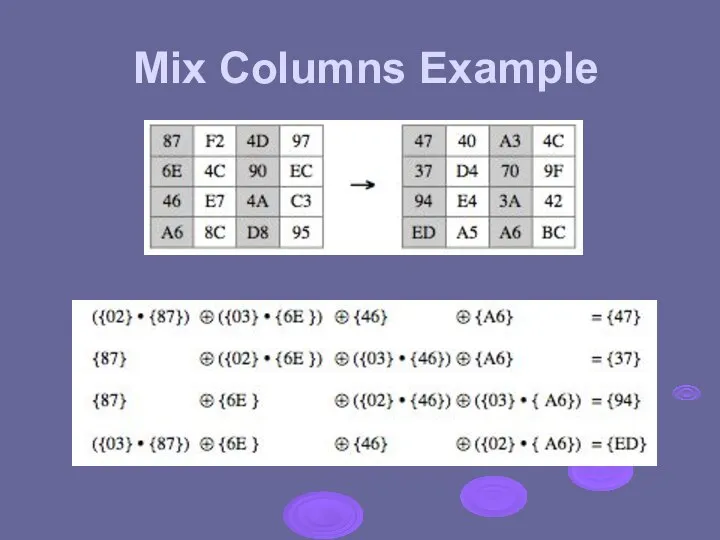
- 16. Mix Columns Example
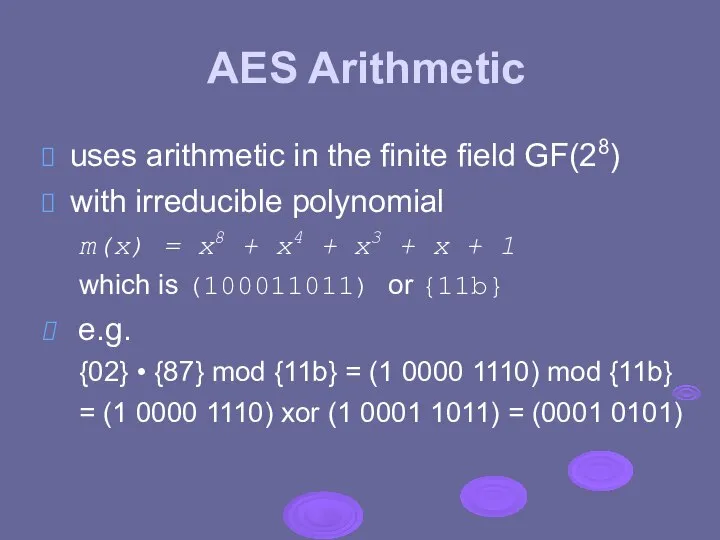
- 17. AES Arithmetic uses arithmetic in the finite field GF(28) with irreducible polynomial m(x) = x8 +
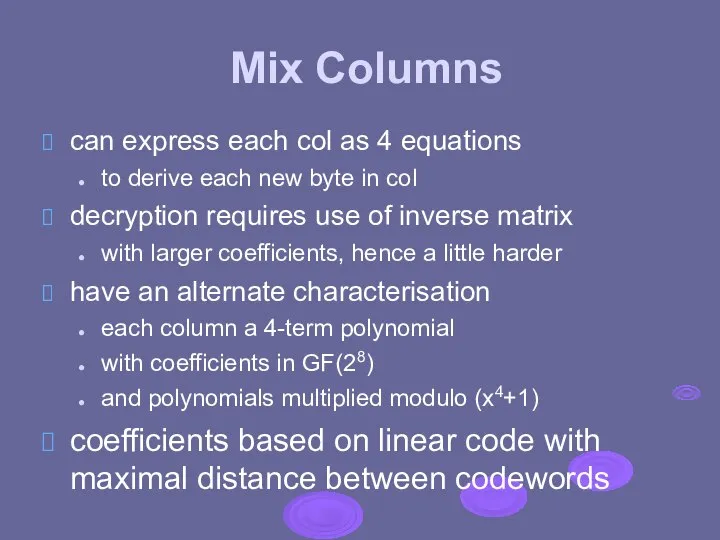
- 18. Mix Columns can express each col as 4 equations to derive each new byte in col
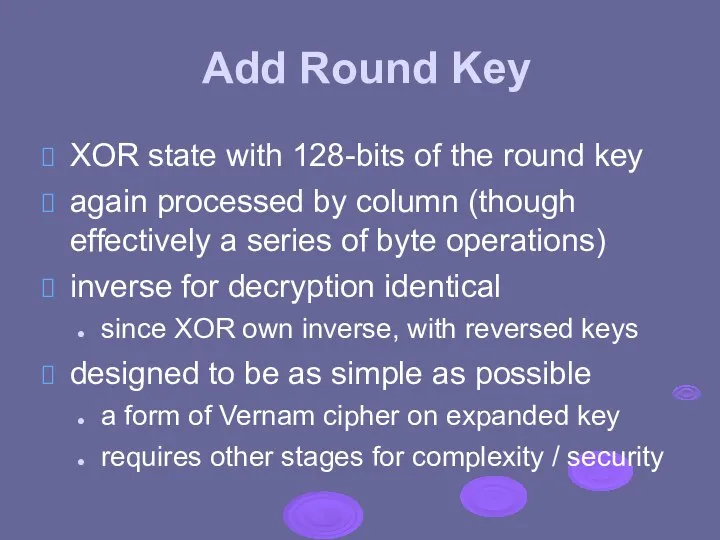
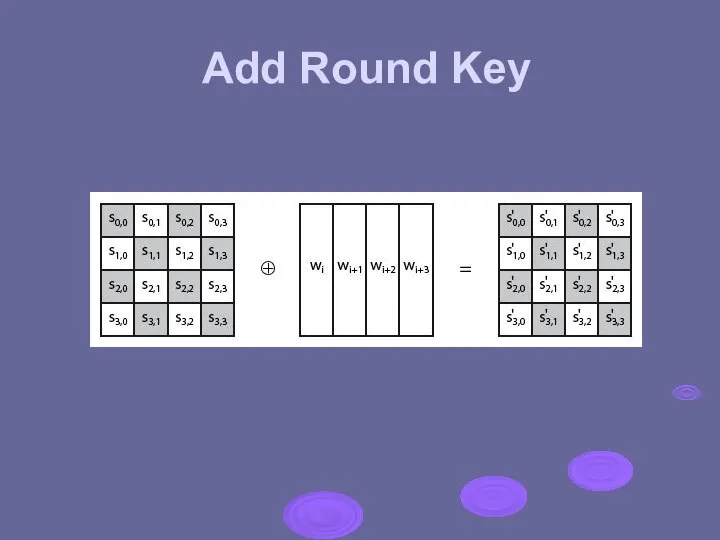
- 19. Add Round Key XOR state with 128-bits of the round key again processed by column (though
- 20. Add Round Key
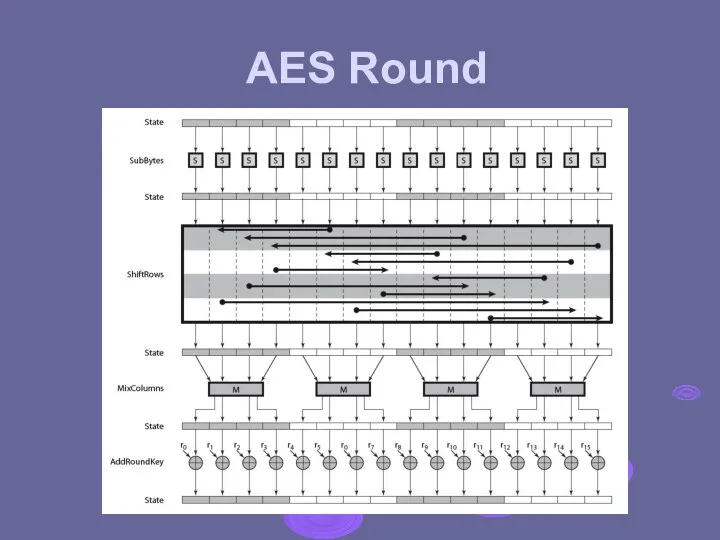
- 21. AES Round
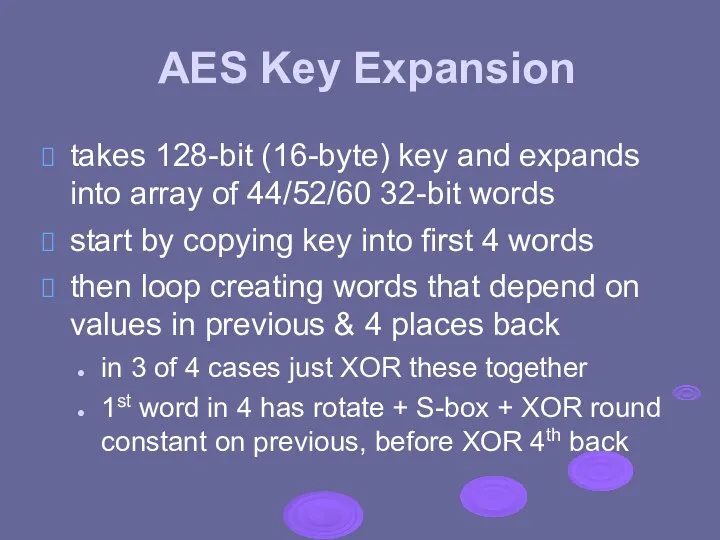
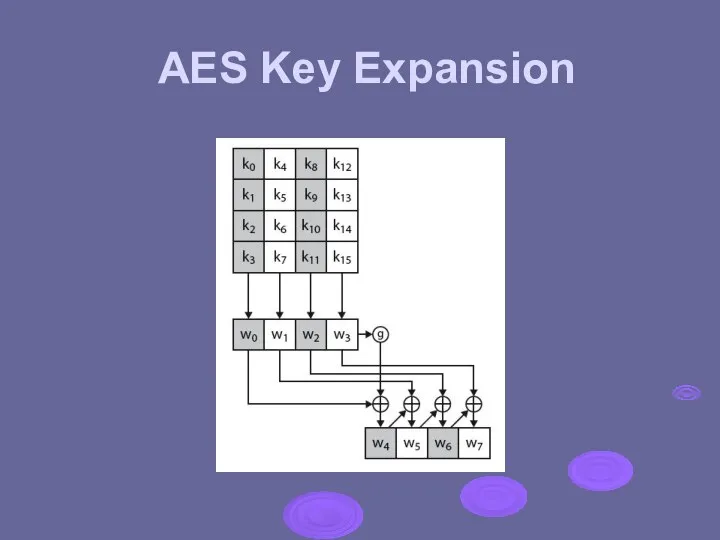
- 22. AES Key Expansion takes 128-bit (16-byte) key and expands into array of 44/52/60 32-bit words start
- 23. AES Key Expansion
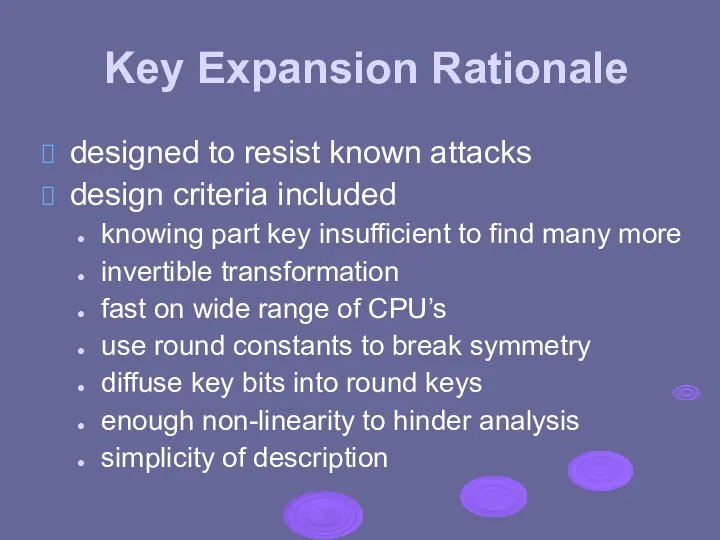
- 24. Key Expansion Rationale designed to resist known attacks design criteria included knowing part key insufficient to
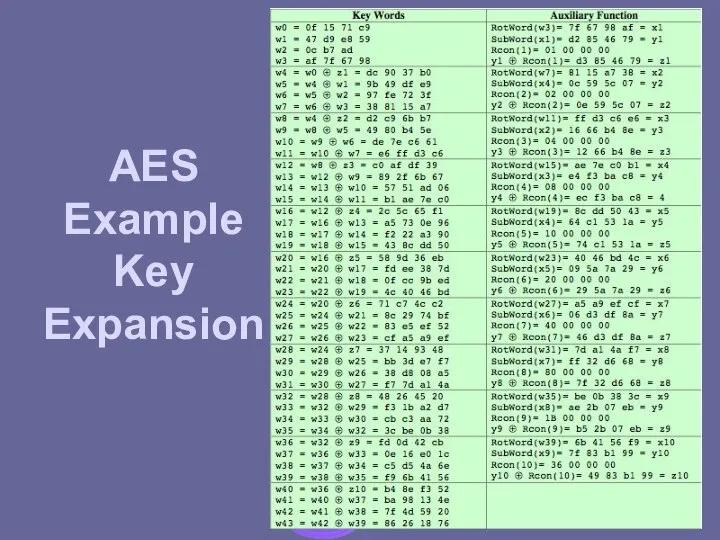
- 25. AES Example Key Expansion
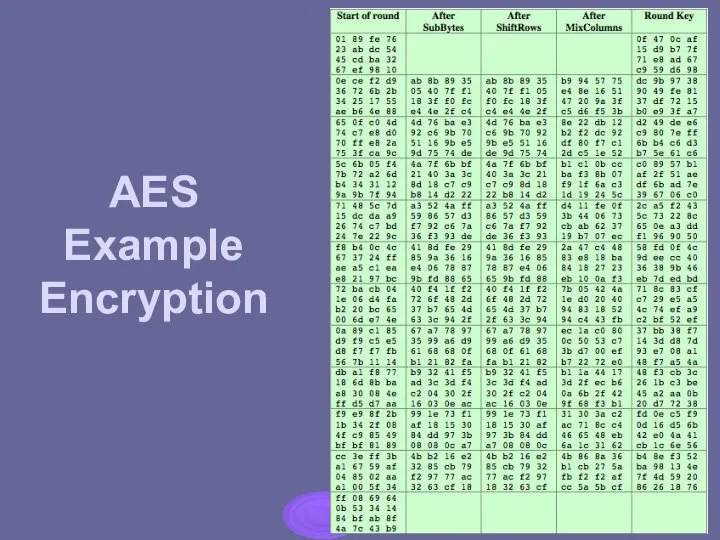
- 26. AES Example Encryption
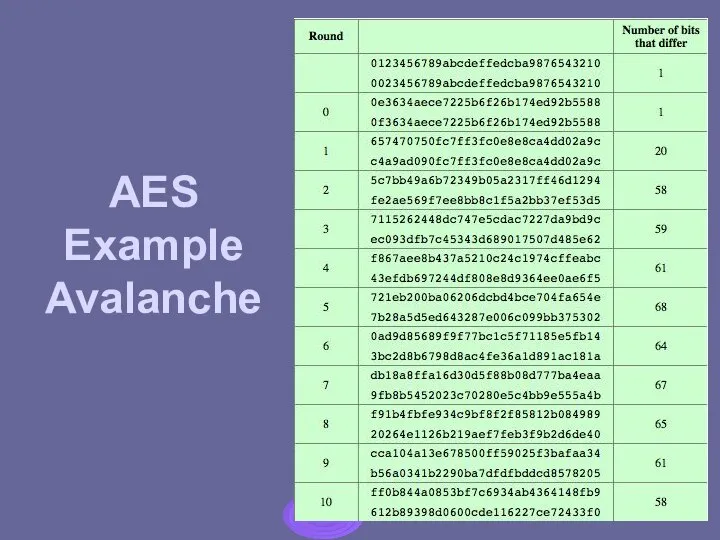
- 27. AES Example Avalanche
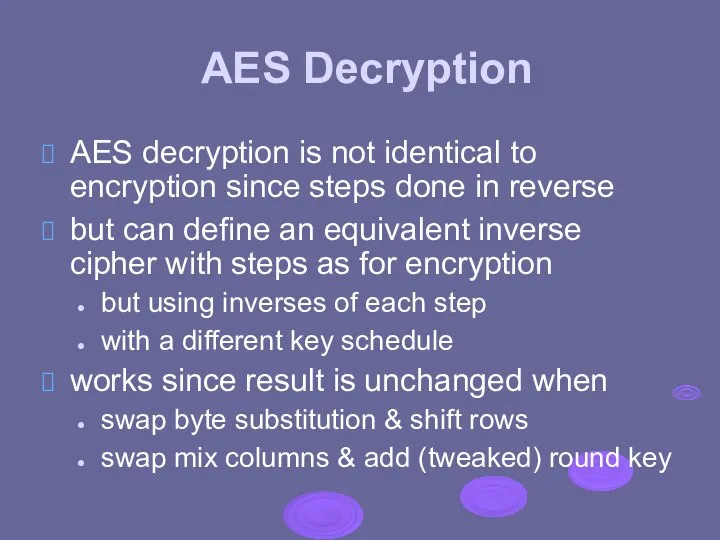
- 28. AES Decryption AES decryption is not identical to encryption since steps done in reverse but can
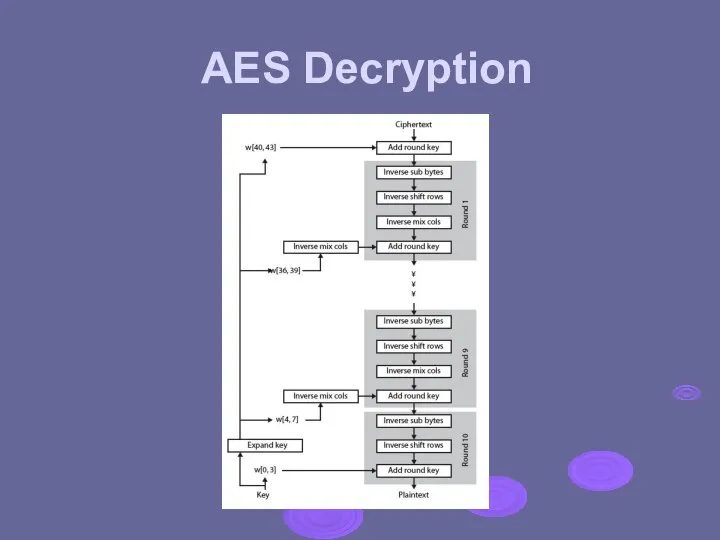
- 29. AES Decryption
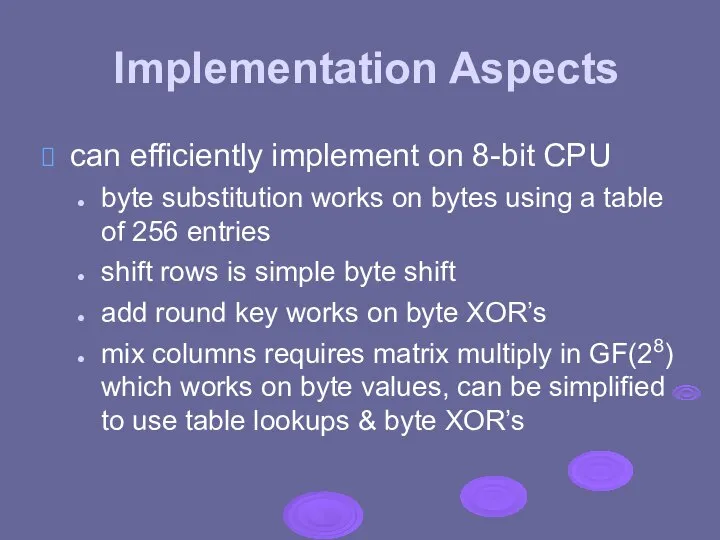
- 30. Implementation Aspects can efficiently implement on 8-bit CPU byte substitution works on bytes using a table
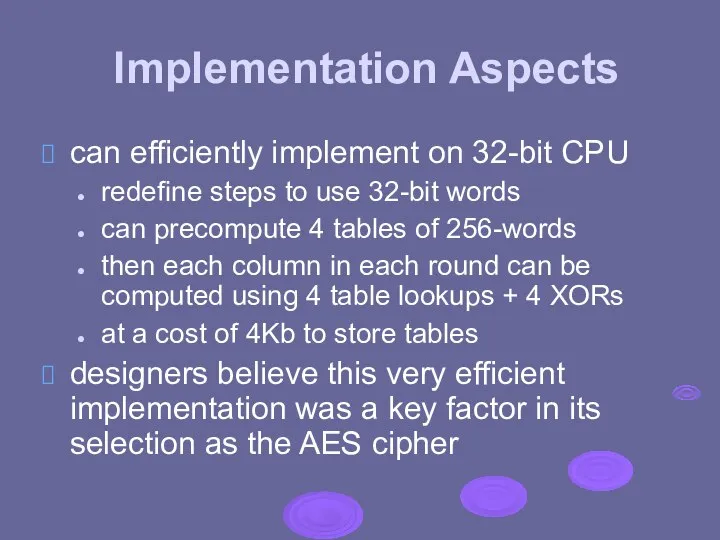
- 31. Implementation Aspects can efficiently implement on 32-bit CPU redefine steps to use 32-bit words can precompute
- 33. Скачать презентацию
 Национальные системы аккредитации в странах Европейского Союза
Национальные системы аккредитации в странах Европейского Союза Однородные члены предложения - презентация для начальной школы
Однородные члены предложения - презентация для начальной школы «Новый курс» Рузвельта
«Новый курс» Рузвельта  Основные характеристики центрального процессора
Основные характеристики центрального процессора Композиторы 18-19 веков
Композиторы 18-19 веков „Wyjątkowy dzień!”. Rzecz o trzecim przykazaniu
„Wyjątkowy dzień!”. Rzecz o trzecim przykazaniu Проект розробки технологічного процесу ремонту вузла живлення телевізора „LG LT-15A15”
Проект розробки технологічного процесу ремонту вузла живлення телевізора „LG LT-15A15” Аттестационная работа. Азбука програмирования (программа элективного курса)
Аттестационная работа. Азбука програмирования (программа элективного курса) Агронавигатор. Система параллельного вождения «Кампус»
Агронавигатор. Система параллельного вождения «Кампус» Халықаралық жеке құқықтың қайнар көздері
Халықаралық жеке құқықтың қайнар көздері Проблемы выживания в походе Автор Санина Настя Ученица 2β класса Гимназия № 6 Руководитель Захарова В.А
Проблемы выживания в походе Автор Санина Настя Ученица 2β класса Гимназия № 6 Руководитель Захарова В.А Опусти свой стакан
Опусти свой стакан Вставка и удаление элементов массива
Вставка и удаление элементов массива Технологии будущего
Технологии будущего Структура и динамика личности Ни В.
Структура и динамика личности Ни В. Культура и мода
Культура и мода Соединения на растянутых связях
Соединения на растянутых связях Новый способ увеличить Ваши продажи через портал РосФирм "Живое" общение с Вашими заказчиками на портале РосФирм
Новый способ увеличить Ваши продажи через портал РосФирм "Живое" общение с Вашими заказчиками на портале РосФирм Значение слова пассия
Значение слова пассия Школьная перемена! Выполнили: Александрова Лиза и Дорошенко Юля. 4(1)класс МОУ «СОШ №41» Тьютор: Гудошкина Нина Павловна
Школьная перемена! Выполнили: Александрова Лиза и Дорошенко Юля. 4(1)класс МОУ «СОШ №41» Тьютор: Гудошкина Нина Павловна Стильная ты
Стильная ты Иконопись в Древней Руси ...её сияющие краски, сильные и яркие, её ритмические силуэты, певучие и мягкие, её просветленные лики, л
Иконопись в Древней Руси ...её сияющие краски, сильные и яркие, её ритмические силуэты, певучие и мягкие, её просветленные лики, л ТЕХНОЛОГИЯ РАЗВИТИЯ ТЕХНОЛОГИЯ РАЗВИТИЯ КРИТИЧЕСКОГО МЫШЛЕНИЯ ПОСРЕДСТВОМ ЧТЕНИЯ И ПИСЬМА
ТЕХНОЛОГИЯ РАЗВИТИЯ ТЕХНОЛОГИЯ РАЗВИТИЯ КРИТИЧЕСКОГО МЫШЛЕНИЯ ПОСРЕДСТВОМ ЧТЕНИЯ И ПИСЬМА Презентация Мирное урегулирование споров в рамках союза
Презентация Мирное урегулирование споров в рамках союза Учитель-логопед высшей категории Филипенко Галина Петровна
Учитель-логопед высшей категории Филипенко Галина Петровна Программирование в среде UNIX. Библиотека PCRE
Программирование в среде UNIX. Библиотека PCRE Образовательные технологии
Образовательные технологии  Таможенная политика Подготовили: Т-114 Галибина Любовь, Карпенко Татьяна
Таможенная политика Подготовили: Т-114 Галибина Любовь, Карпенко Татьяна