Содержание
- 2. Denial-of-service Denial of service (DoS) an action that prevents or impairs the authorized use of networks,
- 3. Classic DoS attacks Flooding ping command Aim of this attack is to overwhelm the capacity of
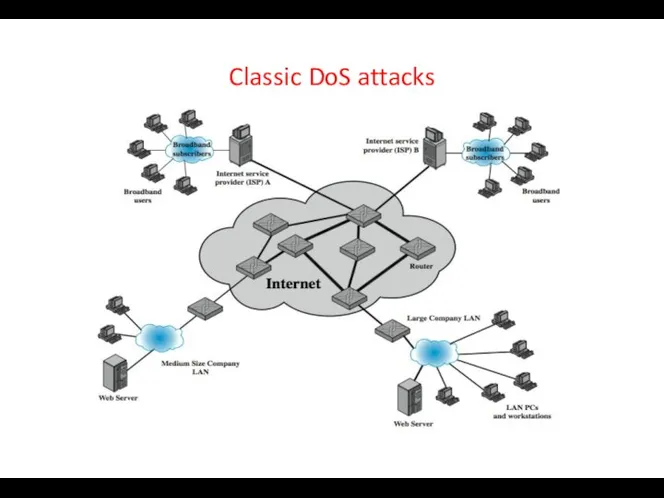
- 4. Classic DoS attacks
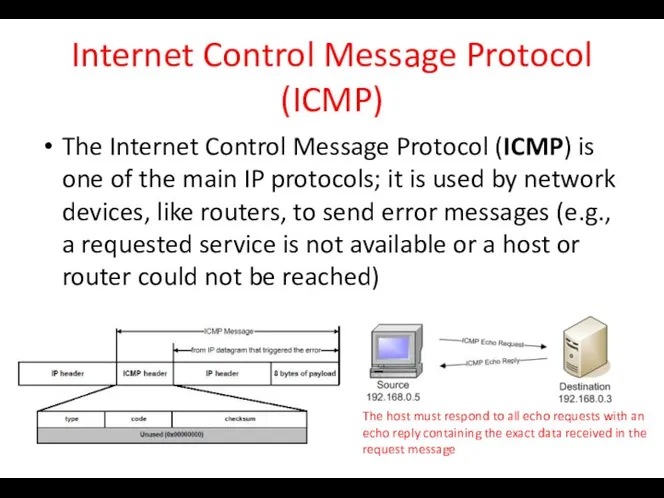
- 5. Internet Control Message Protocol (ICMP) The Internet Control Message Protocol (ICMP) is one of the main
- 6. Source address spoofing Use forged source addresses Usually via the raw socket interface on operating systems
- 7. Backscatter traffic Security researchers (Honeypot Project) advertise blocks of unused IP addresses (no real/legit uses) If
- 8. SYN spoofing Common DoS attack Attacks the ability of a server to respond to future connection
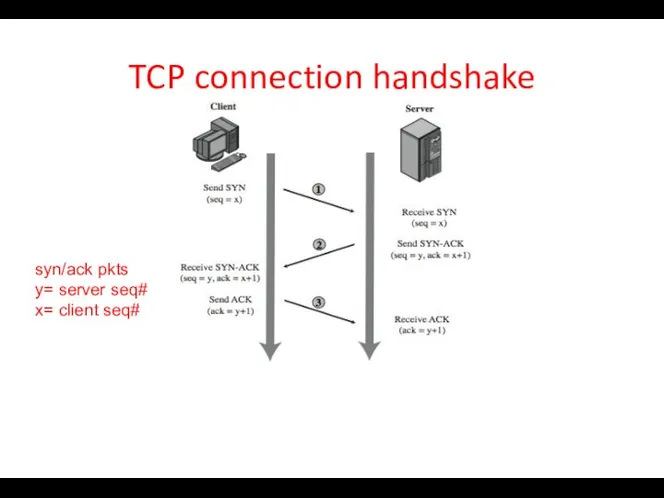
- 9. TCP connection handshake syn/ack pkts y= server seq# x= client seq#
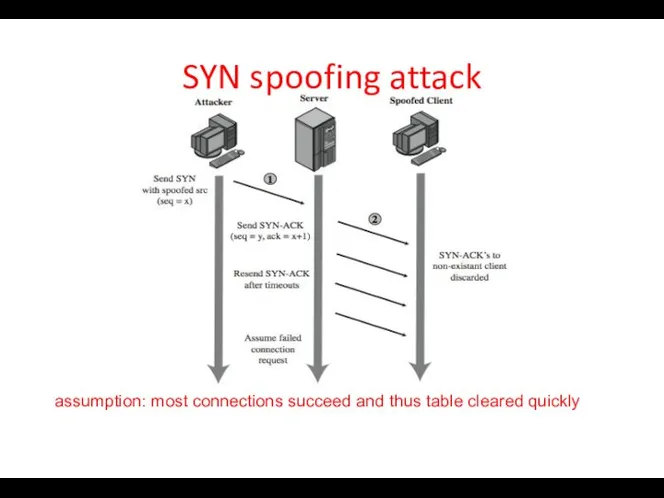
- 10. SYN spoofing attack assumption: most connections succeed and thus table cleared quickly
- 11. SYN spoofing attack: attacker’s source Attacker often uses either random source addresses (addresses that may not
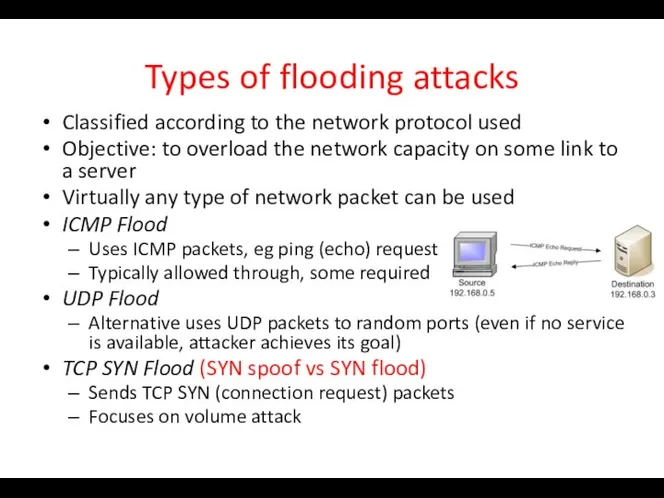
- 12. Types of flooding attacks Classified according to the network protocol used Objective: to overload the network
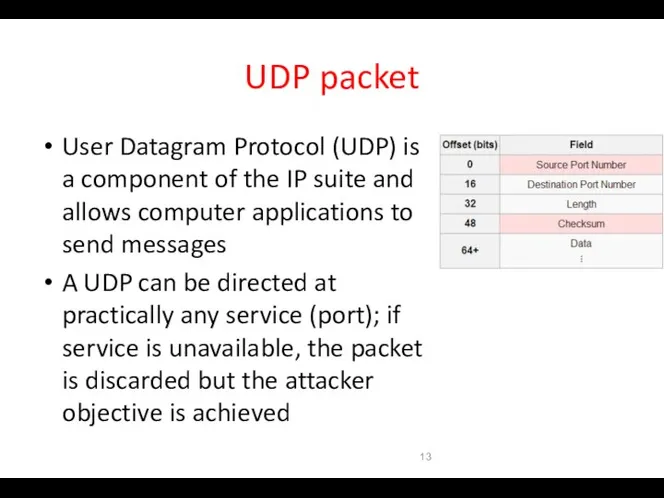
- 13. UDP packet User Datagram Protocol (UDP) is a component of the IP suite and allows computer
- 14. Distributed DoS attacks Have limited volume if single source used Multiple systems allow much higher traffic
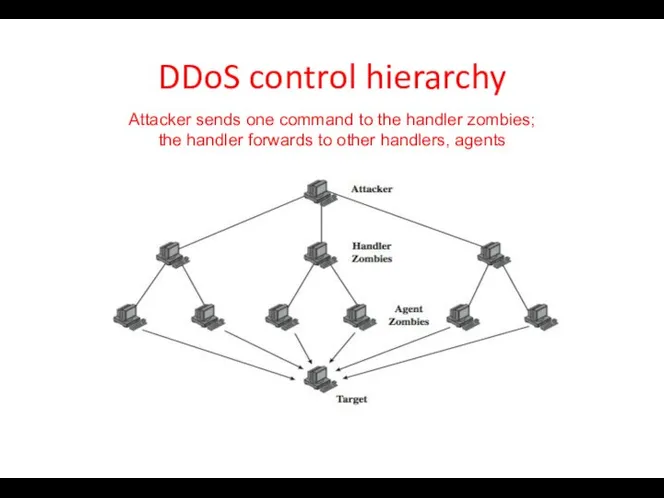
- 15. DDoS control hierarchy Attacker sends one command to the handler zombies; the handler forwards to other
- 16. Application-based bandwidth attacks Force the victim system to execute resource-consuming operations (e.g., searches, complex DB queries)
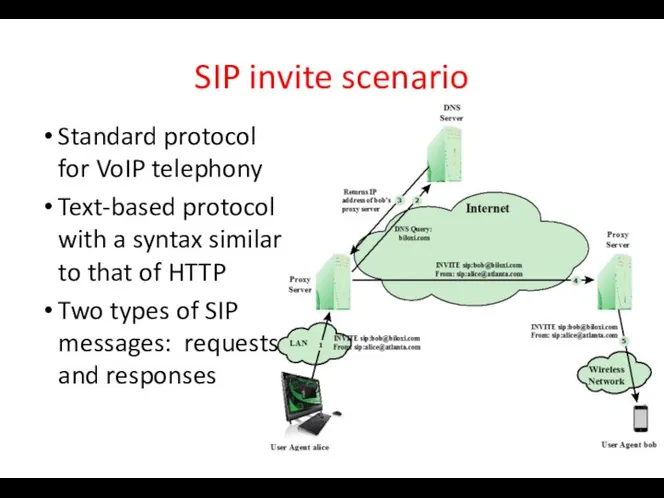
- 17. SIP invite scenario Standard protocol for VoIP telephony Text-based protocol with a syntax similar to that
- 18. HTTP-based attacks Slowloris: On each connection, it sends an incomplete request that does not include the
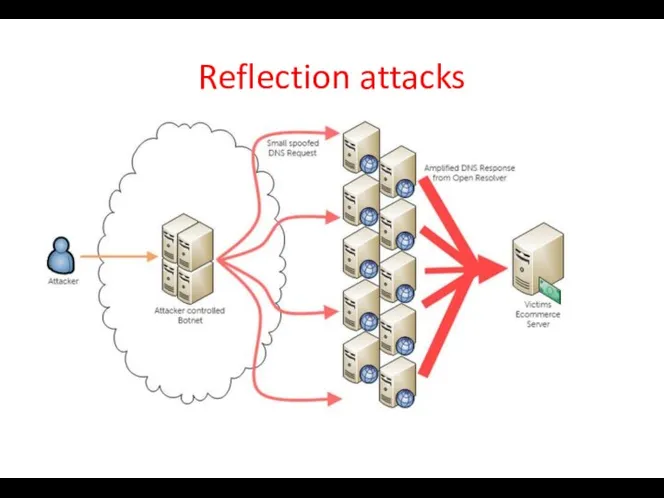
- 19. Reflection attacks Attacker sends packets to a known service on the intermediary with a “spoofed source
- 20. Reflection attacks
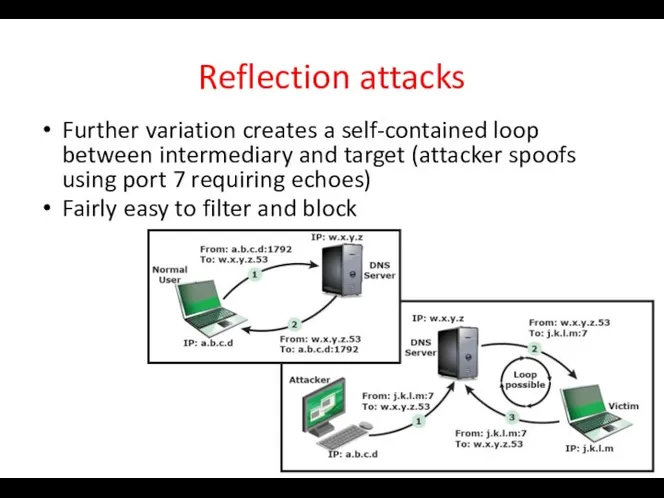
- 21. Reflection attacks Further variation creates a self-contained loop between intermediary and target (attacker spoofs using port
- 22. DNS amplification attacks Use packets directed at a legitimate DNS server as the intermediary system Attacker
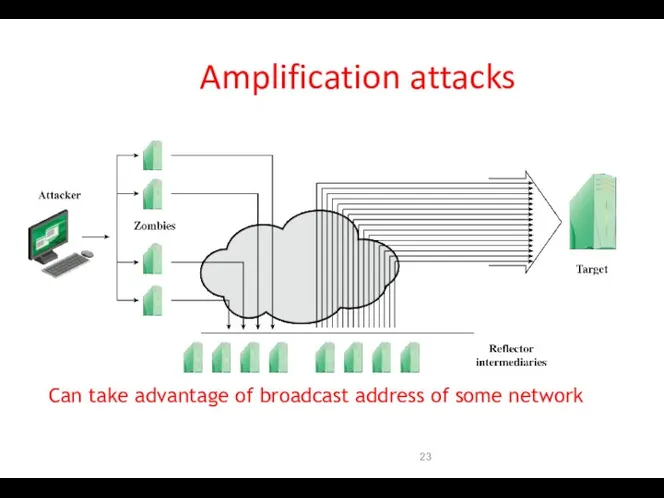
- 23. Amplification attacks Can take advantage of broadcast address of some network
- 24. Four lines of defense against DDoS attacks Attack prevention and preemption (before attack) Attack detection and
- 25. DoS attack prevention Block spoofed source addresses On routers as close to source as possible Filters
- 26. Attack prevention Rate controls in upstream distribution nets On specific packets types e.g. some ICMP, some
- 27. Attack prevention Block IP directed broadcasts Block suspicious services and combinations Manage application attacks with a
- 28. Responding to attacks Good incidence response plan Details on how to contact technical personal for ISP
- 29. Responding to attacks Identify type of attack Capture and analyze packets Design filters to block attack
- 31. Скачать презентацию
 « Единственная известная мне роскошь – это роскошь человеческого общения» Антуан Сент - Экзюпери. - презентация
« Единственная известная мне роскошь – это роскошь человеческого общения» Антуан Сент - Экзюпери. - презентация Основи будови радіостанцій. Види модуляції ВЧ-сигналу (Лекція 3.1)
Основи будови радіостанцій. Види модуляції ВЧ-сигналу (Лекція 3.1) Якутский эпос - олонхо
Якутский эпос - олонхо Технические характеристики мониторов
Технические характеристики мониторов От ключевых компетенций- к успеху в жизни. формирование ключевых компетенций на уроках химии Учитель химии МКОУ Жуланская СОШ
От ключевых компетенций- к успеху в жизни. формирование ключевых компетенций на уроках химии Учитель химии МКОУ Жуланская СОШ Что не является видом изобразительного искусства
Что не является видом изобразительного искусства Литературная викторина Автор презентации Клюквина В А
Литературная викторина Автор презентации Клюквина В А Организация перевозки багажа, груза, почты
Организация перевозки багажа, груза, почты prezentatsiya3_ruz.vaz_
prezentatsiya3_ruz.vaz_ Правительство Российской Федерации: конституционно-правовой статус. Тема 8
Правительство Российской Федерации: конституционно-правовой статус. Тема 8 Религия Средневековья
Религия Средневековья Образ Александра Невского в русской литературе и исскустве
Образ Александра Невского в русской литературе и исскустве Роль цвета в портрете
Роль цвета в портрете Долгожданный дан звонок, Начинается урок!
Долгожданный дан звонок, Начинается урок!  ТЕХНОЛОГИЧЕСКИЙ ПОТЕНЦИАЛ РОССИИ Карташова Галина Т-093
ТЕХНОЛОГИЧЕСКИЙ ПОТЕНЦИАЛ РОССИИ Карташова Галина Т-093  Архыз - 2018. Карачаево-Черкесия
Архыз - 2018. Карачаево-Черкесия Изображение и обозначение резьбы
Изображение и обозначение резьбы Гимнастика для мозга
Гимнастика для мозга Авторское право
Авторское право Античная наука
Античная наука  Функциональная анатомия сердца и пороки его развития
Функциональная анатомия сердца и пороки его развития Состав архитектурного проекта
Состав архитектурного проекта Человек познает мир обществознание 6 класс
Человек познает мир обществознание 6 класс  Основы языка ассемблер. Использование массивов
Основы языка ассемблер. Использование массивов защита прав человека
защита прав человека Некариозные поражения
Некариозные поражения Возможности системы DELO
Возможности системы DELO Презентация Концепция долгосрочного социально-экономического развития Российской Федерации
Презентация Концепция долгосрочного социально-экономического развития Российской Федерации