Содержание
- 2. IEEE 802.11 IEEE 802 committee for LAN standards IEEE 802.11 formed in 1990’s charter to develop
- 3. IEEE 802 Terminology Access point (AP) : Any entity that has station functionality and provides access
- 4. IEEE 802 Terminology Extended service set (ESS): A set of one or more interconnected BSSs and
- 5. Wi-Fi Alliance 802.11b first broadly accepted standard Wireless Ethernet Compatibility Alliance (WECA) industry consortium formed 1999
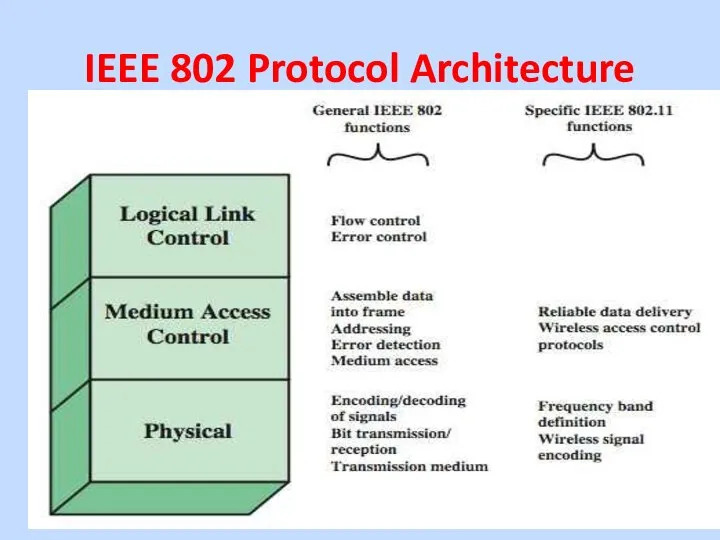
- 6. IEEE 802 Protocol Architecture
- 7. IEEE 802 Protocol Architecture IEEE 802 physical layer includes: • Encoding/decoding of signals • Transmission/reception •
- 8. IEEE 802 Protocol Architecture Media Access Control (MAC) layer controls access to the transmission medium: •
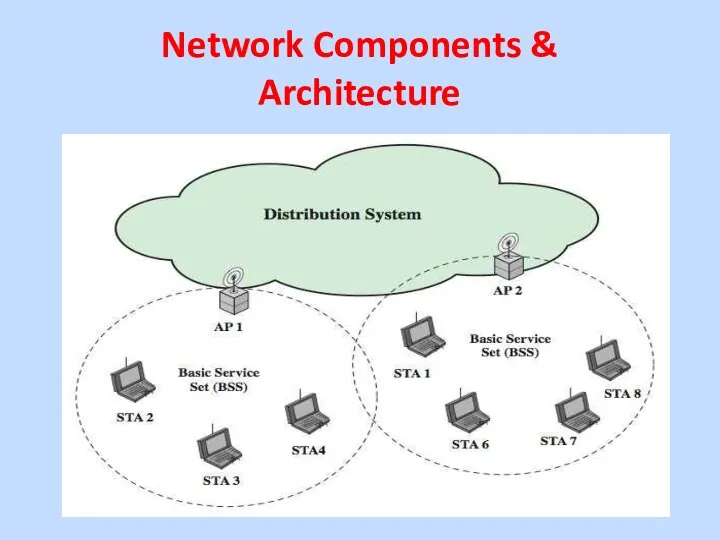
- 9. Network Components & Architecture
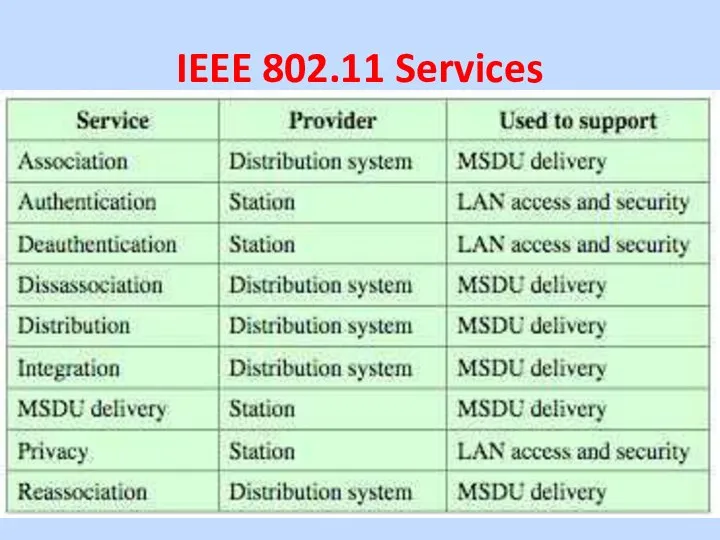
- 10. IEEE 802.11 Services
- 11. IEEE 802.11 Services (9 Services) The service provider can be either the station or the DS:
- 12. IEEE 802.11 Services (9 Services) Three services control IEEE 802.11 LAN access and confidentiality: –Authentication, Deauthentication
- 13. IEEE 802.11 Services (9 Services) MSDU delivery, basic service, in which the information that is delivered
- 14. IEEE 802.11 Services (9 Services) Association, establishes an initial association between a station and an AP.
- 15. 802.11 Wireless LAN Security wireless traffic can be monitored by any radio in range, not physically
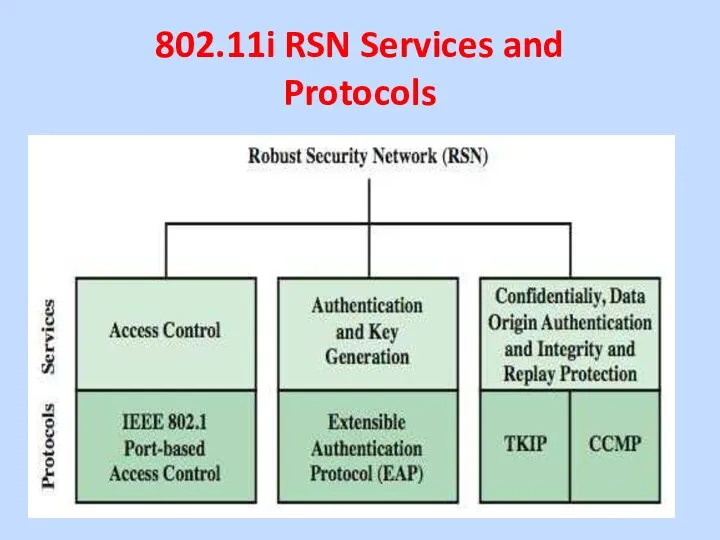
- 16. 802.11i RSN Services and Protocols
- 17. 802.11i RSN Services and Protocols The 802.11i RSN security specification defines the following services: • Authentication:
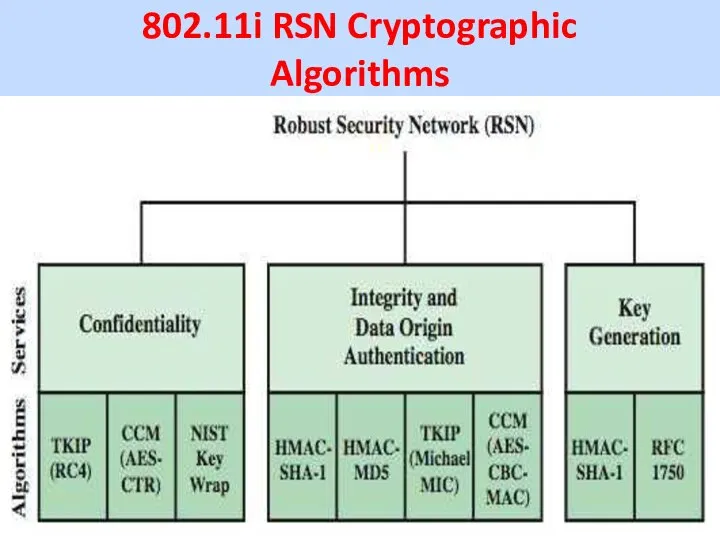
- 18. 802.11i RSN Cryptographic Algorithms
- 19. 802.11i Phases of Operation
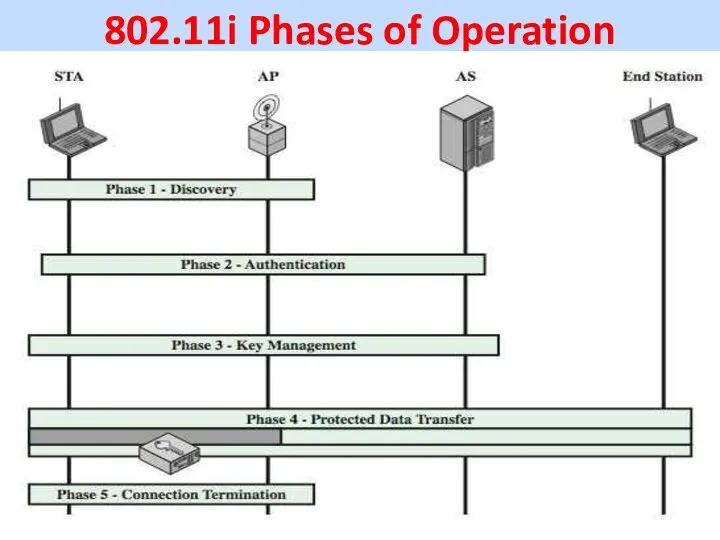
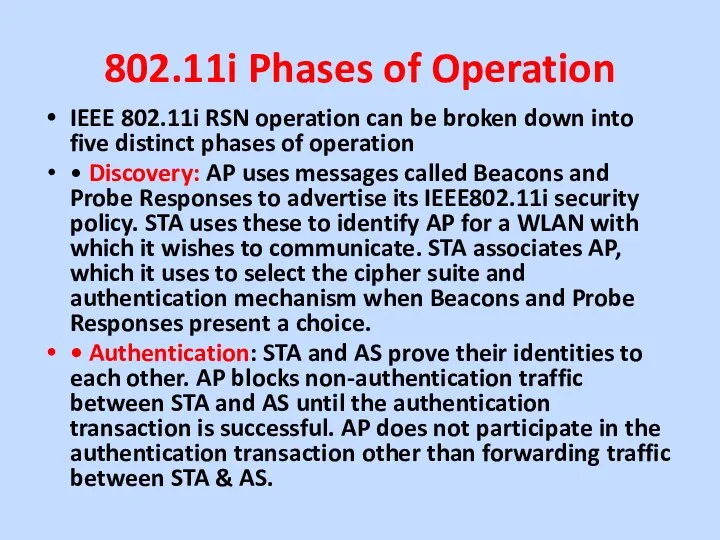
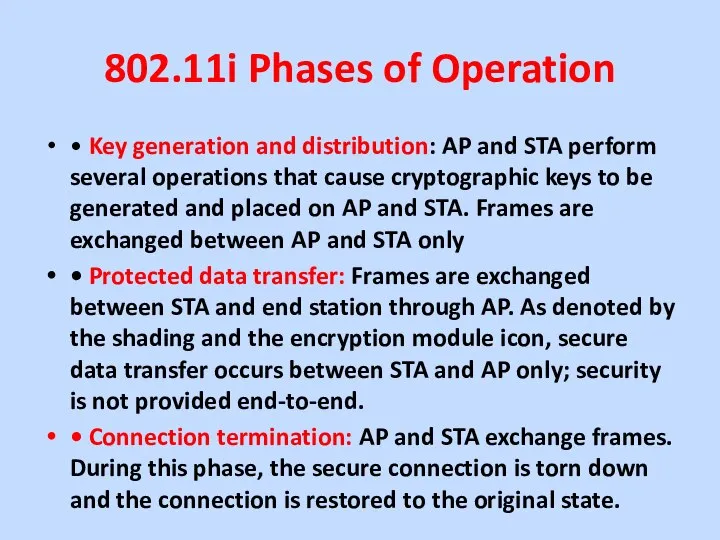
- 20. 802.11i Phases of Operation IEEE 802.11i RSN operation can be broken down into five distinct phases
- 21. 802.11i Phases of Operation • Key generation and distribution: AP and STA perform several operations that
- 22. 802.11i Discovery and Authentication Phases The Discovery phase is for an STA and an AP to
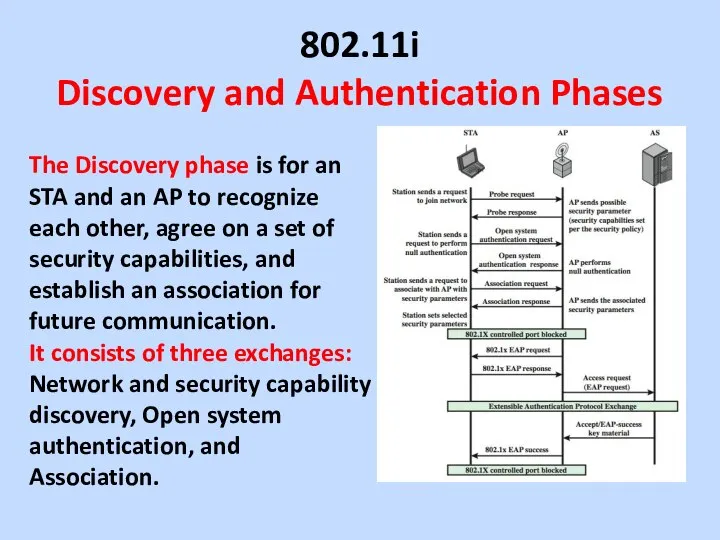
- 23. 802.11i Discovery and Authentication Phases The authentication phase enables mutual authentication between an STA and an
- 24. IEEE 802.1X Access Control Approach
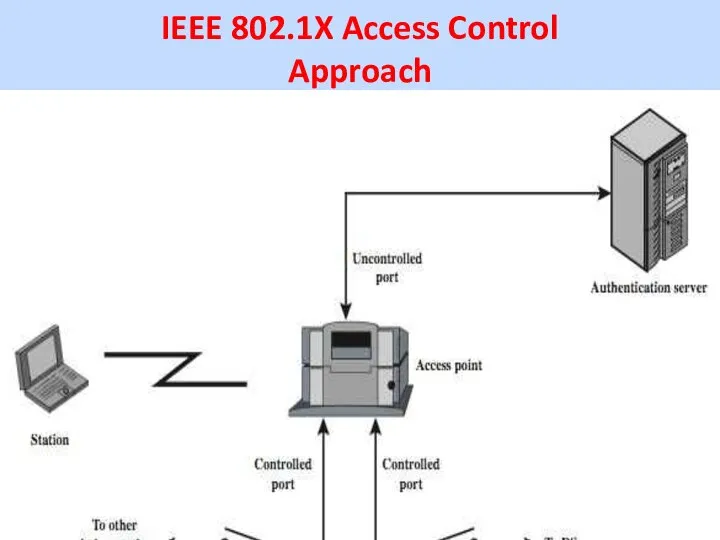
- 25. IEEE 802.1X Access Control Approach IEEE 802.11i uses the Extensible Authentication Protocol (EAP). Before wireless station
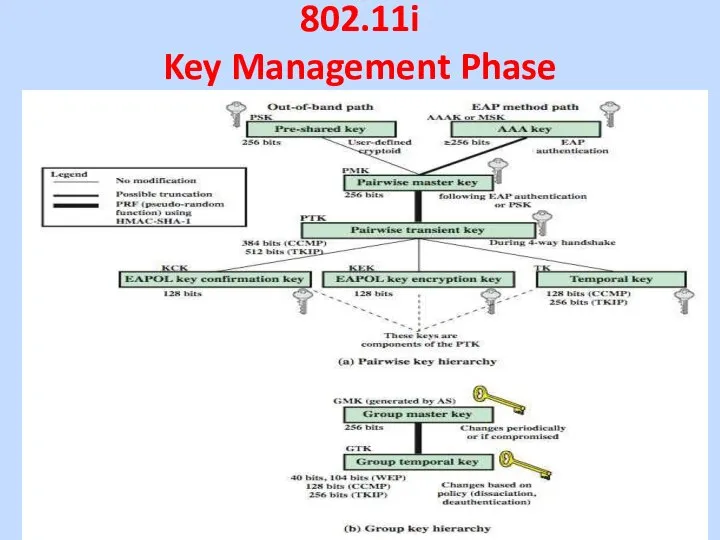
- 26. 802.11i Key Management Phase
- 27. 802.11i Key Management Phase 802.11i Key Management Phase • AP controlled ports remain blocked until the
- 28. 802.11i Key Management Phase • Pre-shared key (PSK) A secret key shared by AP and STA
- 29. 802.11i Key Management Phase
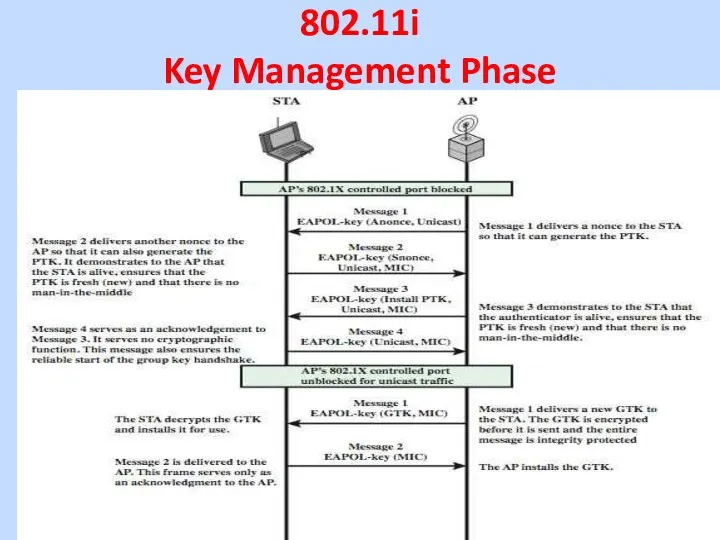
- 30. 802.11i Key Management Phase 4-way handshake exchange MPDU for distributing pairwise keys. STA and AP confirm
- 31. 802.11i Protected Data Transfer Phase have two schemes for protecting data Temporal Key Integrity Protocol (TKIP)
- 32. Wireless Application Protocol (WAP) •(WAP) is a universal, open standard developed by the WAP Forum to
- 33. Wireless Application Protocol (WAP) •WAP specification includes: • A programming model based on the WWW Programming
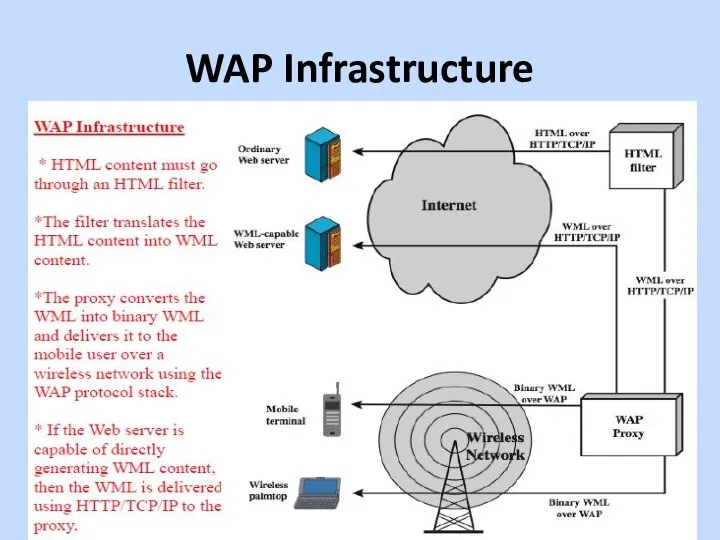
- 34. WAP Infrastructure
- 35. Summary have considered: - IEEE 802.11 Wireless LANs - protocol overview and security - Wireless Application
- 37. Скачать презентацию
 Подготовили студентки группы 7282 Соловьёва Кристина и Кузьмина Мария
Подготовили студентки группы 7282 Соловьёва Кристина и Кузьмина Мария Петр Смирнов
Петр Смирнов Система и организация государственной службы в Российской Федерации. Правовые основы государственной службы
Система и организация государственной службы в Российской Федерации. Правовые основы государственной службы Амальфи
Амальфи ТЕХНОЛОГИЯ ФОРМИРОВАНИЯ ТЕМПОРИТМИЧЕСКОЙ ОРГАНИЗАЦИИ РЕЧИ ПРИ ЗАИКАНИИ
ТЕХНОЛОГИЯ ФОРМИРОВАНИЯ ТЕМПОРИТМИЧЕСКОЙ ОРГАНИЗАЦИИ РЕЧИ ПРИ ЗАИКАНИИ  Презентация Административные наказания: понятие и виды
Презентация Административные наказания: понятие и виды Геополитический проект СССР
Геополитический проект СССР  Профилактика подросткового суицида Prezentacii.com
Профилактика подросткового суицида Prezentacii.com  Правовий режим земель сільськогосподарського призначення
Правовий режим земель сільськогосподарського призначення ИТ менеджмент: Управление ИТ проектом глазами бизнеса
ИТ менеджмент: Управление ИТ проектом глазами бизнеса Свойства Свойства числовых неравенств (8 класс)
Свойства Свойства числовых неравенств (8 класс) Твёрдые, кристалические и аморфные тела
Твёрдые, кристалические и аморфные тела Алгоритмизация и программирование
Алгоритмизация и программирование евпрм
евпрм  Здоровый образ жизни
Здоровый образ жизни Государственное общеобразовательное учреждение средняя общеобразовательная школа № 337 Невского района Санкт-Петербурга П
Государственное общеобразовательное учреждение средняя общеобразовательная школа № 337 Невского района Санкт-Петербурга П Розборка ноутбука HP Pavilion G6
Розборка ноутбука HP Pavilion G6 Проблема биосовместимости (лекция 3)
Проблема биосовместимости (лекция 3) Waterproof Cable Glands - VSM Plast
Waterproof Cable Glands - VSM Plast Вебинар: Постановка на учет обособленных подразделений Поправки в ч. 1 НК РФ по Федеральному закону от 27.07.10 № 229-ФЗ
Вебинар: Постановка на учет обособленных подразделений Поправки в ч. 1 НК РФ по Федеральному закону от 27.07.10 № 229-ФЗ урок 1
урок 1 Презентация на тему "Давай посчитаем! Вертолёты" - скачать презентации по Педагогике
Презентация на тему "Давай посчитаем! Вертолёты" - скачать презентации по Педагогике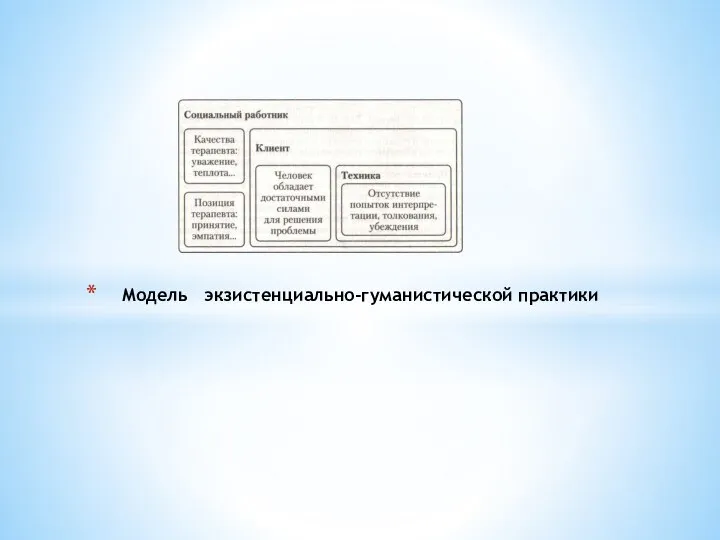 Модель экзистенциально-гуманистической практики
Модель экзистенциально-гуманистической практики Презентация Российский рынок риса в 1990-2013 гг
Презентация Российский рынок риса в 1990-2013 гг  Культурологія. Магістерська програма
Культурологія. Магістерська програма Плотницкие приемы. Эволюция развития
Плотницкие приемы. Эволюция развития Главная тайна растений - презентация для начальной школы_
Главная тайна растений - презентация для начальной школы_ УМК «Школа России» По стране Сказок
УМК «Школа России» По стране Сказок