Содержание
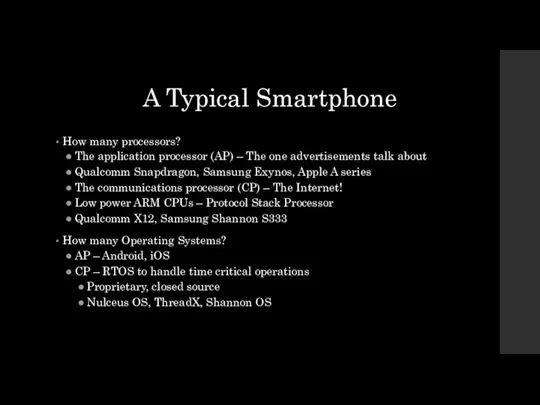
- 2. A Typical Smartphone How many processors? The application processor (AP) – The one advertisements talk about
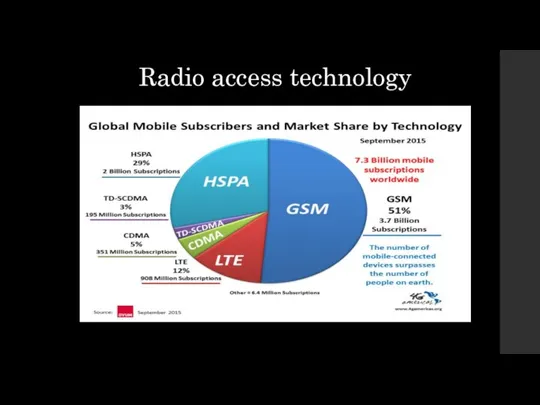
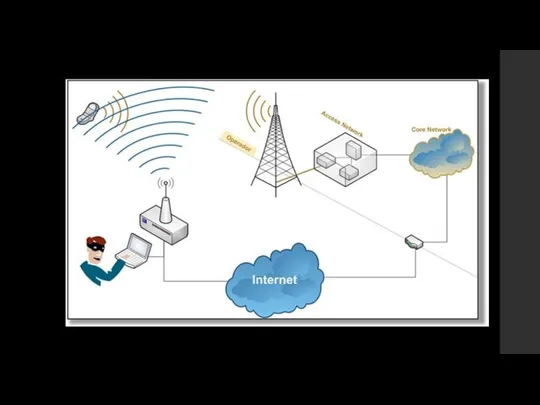
- 4. Radio access technology
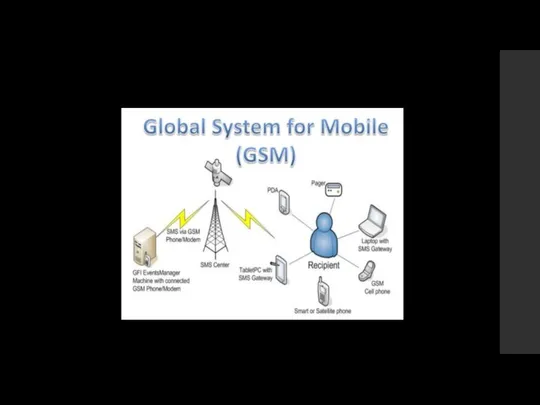
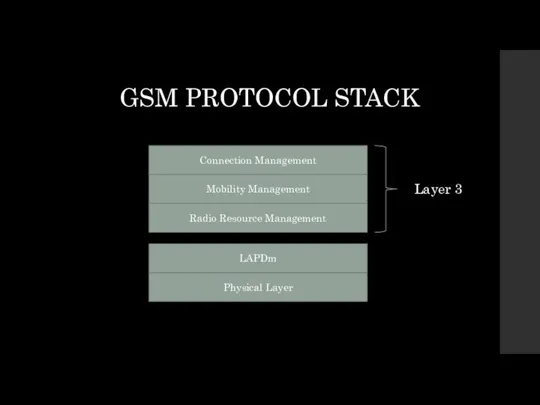
- 6. Physical Layer LAPDm Radio Resource Management Mobility Management Connection Management Layer 3 GSM PROTOCOL STACK
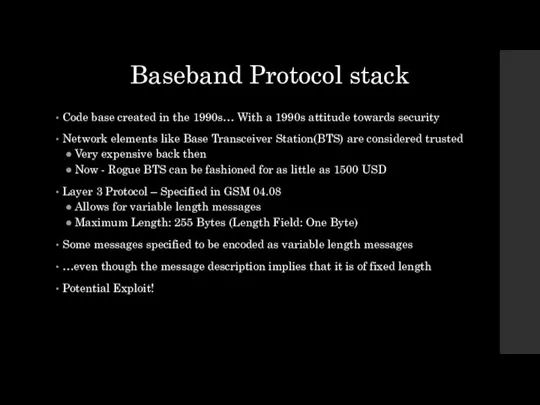
- 7. Baseband Protocol stack Code base created in the 1990s… With a 1990s attitude towards security Network
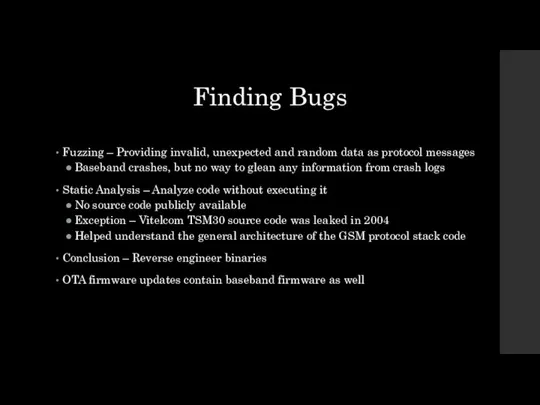
- 8. Finding Bugs Fuzzing – Providing invalid, unexpected and random data as protocol messages Baseband crashes, but
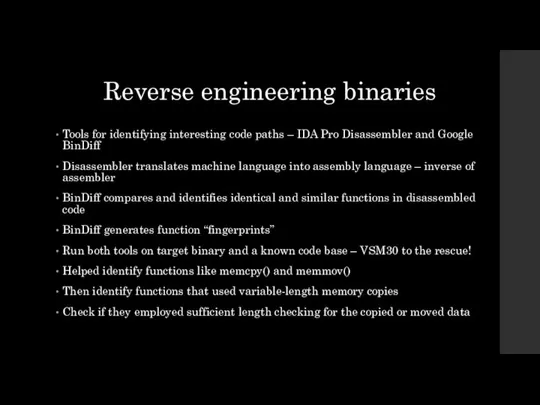
- 9. Reverse engineering binaries Tools for identifying interesting code paths – IDA Pro Disassembler and Google BinDiff
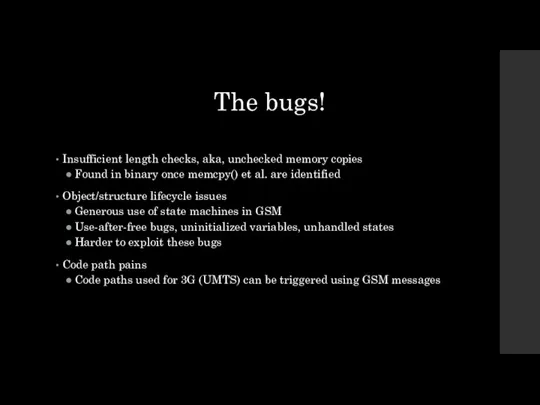
- 10. The bugs! Insufficient length checks, aka, unchecked memory copies Found in binary once memcpy() et al.
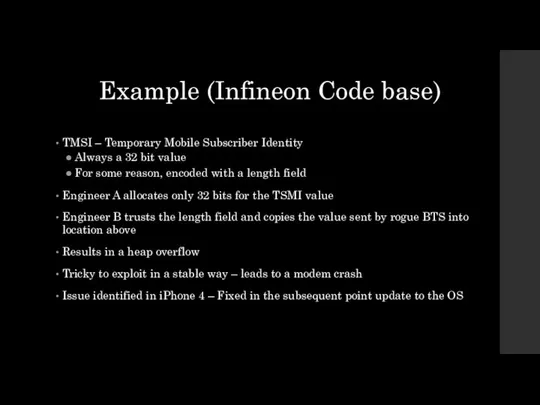
- 11. Example (Infineon Code base) TMSI – Temporary Mobile Subscriber Identity Always a 32 bit value For
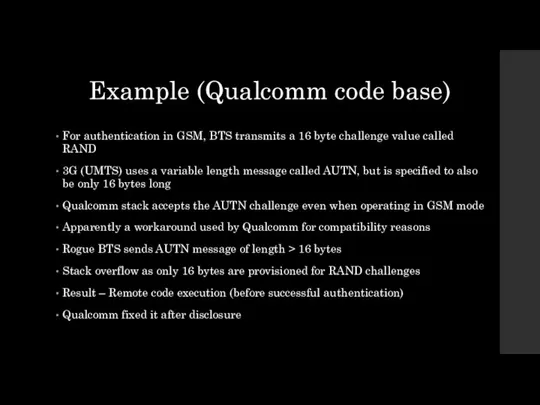
- 12. Example (Qualcomm code base) For authentication in GSM, BTS transmits a 16 byte challenge value called
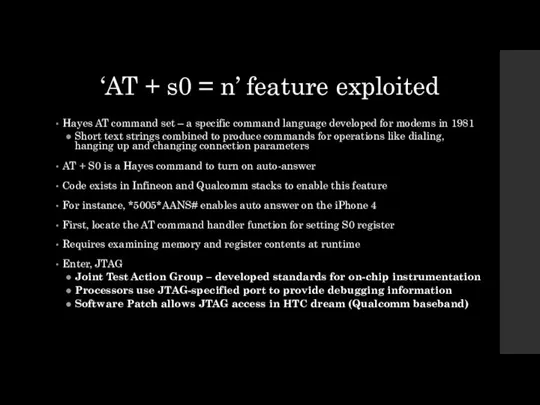
- 13. ‘AT + s0 = n’ feature exploited Hayes AT command set – a specific command language
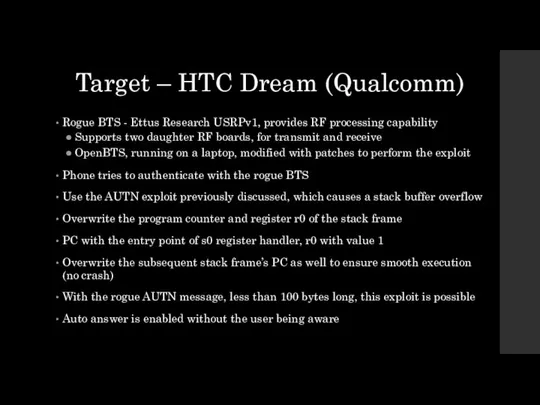
- 15. Target – HTC Dream (Qualcomm) Rogue BTS - Ettus Research USRPv1, provides RF processing capability Supports
- 16. Impact Place Rogue BTS in crowded/sensitive areas Audio routing on most chipsets is done on baseband
- 17. Solutions? Open source baseband stack Quicker at identifying bugs But still hard to patch them as
- 19. Скачать презентацию
 Отдел маркетинга и инноваций Школа качества и управления
Отдел маркетинга и инноваций Школа качества и управления Принципиальные схемы установок. Применение метода лазерной дифракции
Принципиальные схемы установок. Применение метода лазерной дифракции Маскировка БЖД
Маскировка БЖД Павел Степанович Нахимов
Павел Степанович Нахимов Разработка системы мероприятий по эксплуатации и техническому обслуживанию песочной системы тепловоза 2ТЭ-116
Разработка системы мероприятий по эксплуатации и техническому обслуживанию песочной системы тепловоза 2ТЭ-116 Коклюш – семинар часть3
Коклюш – семинар часть3 Роль финансовой сферы в трансформации рисков и неопределенности в современной экономике Финансовая академия при Прав
Роль финансовой сферы в трансформации рисков и неопределенности в современной экономике Финансовая академия при Прав Language Club "La tua Italia"
Language Club "La tua Italia" Субъективная сторона преступления. (Тема 8)
Субъективная сторона преступления. (Тема 8) Организация и проведение аттестации педагогических работников
Организация и проведение аттестации педагогических работников Комплекс подготовительных упражнений «Комплекс Б» Э.Я. Золотаревой
Комплекс подготовительных упражнений «Комплекс Б» Э.Я. Золотаревой Деньги, кредит, банки К.э.н., доцент Демина Надежда Константиновна
Деньги, кредит, банки К.э.н., доцент Демина Надежда Константиновна  Презентация "Родословная матрешки" - скачать презентации по МХК
Презентация "Родословная матрешки" - скачать презентации по МХК Использование 3D-принтера
Использование 3D-принтера Обучение детей ходьбе на лыжах
Обучение детей ходьбе на лыжах Духовно-нравственное воспитание школьников
Духовно-нравственное воспитание школьников  АКТУАЛЬНЫЕ НОВОСТИ. Кайдакова и Зрелова Т-113
АКТУАЛЬНЫЕ НОВОСТИ. Кайдакова и Зрелова Т-113 Das Land Deutschland, seine schönsten Städte und Feiertage
Das Land Deutschland, seine schönsten Städte und Feiertage Регуляция соматических функций
Регуляция соматических функций Антониево-Сийский СвятоТроицкий мужской монастырь
Антониево-Сийский СвятоТроицкий мужской монастырь Моя специальность-экономист
Моя специальность-экономист Система Л.В Занкова Если вы владеете знанием, дайте другим зажечь от него свои светильники. Томас Фуллер
Система Л.В Занкова Если вы владеете знанием, дайте другим зажечь от него свои светильники. Томас Фуллер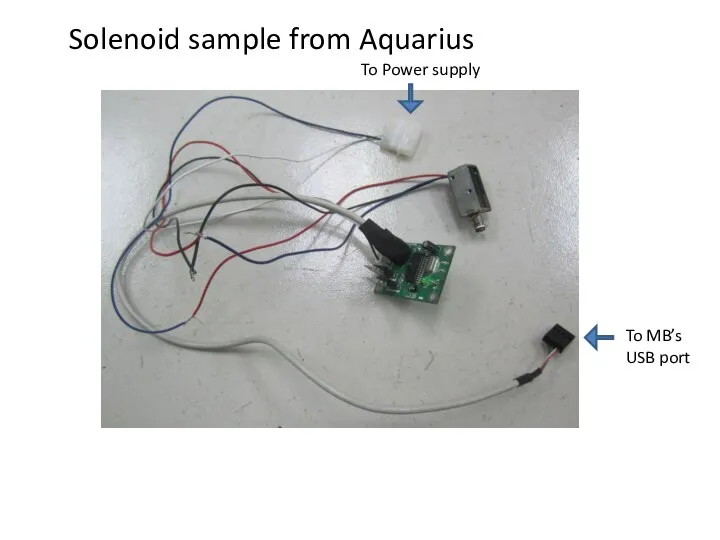 Test result from Aquarius's solenoid lock sample
Test result from Aquarius's solenoid lock sample Математизация и информатизация экспертной деятельности
Математизация и информатизация экспертной деятельности лекция 6
лекция 6 Коферменты и простетические группы
Коферменты и простетические группы  АДАПТАЦИЯ- процесс развития приспособительных реакций организма в ответ на новые для него условия.
АДАПТАЦИЯ- процесс развития приспособительных реакций организма в ответ на новые для него условия. Презентация Ненужные изобретения
Презентация Ненужные изобретения